Lessons learned from improving full-text search at Snyk with Elasticsearch
Elasticsearch is a popular open source search engine. Because of its real-time speeds and robust API, it’s a popular choice among developers that need to add full-text search capabilities in their projects. Aside from being generally popular, it’s also the engine we’re currently moving our Snyk reports functionality for issues! And once we have everything tuned in issues, we’ll start using Elasticsearch in other reporting areas.
Using Veracode From the Command Line in Cloud9 IDE
Hello, Clint Pollock, principal solutions architect here to explain how to use Veracode completely from a command prompt in your IDE or CI/CD system. I’m going to teach you how to submit a static policy scan and a static sandbox scan. Then, I’m going to clean up some builds using the API, submit a static pipeline scan, a software composition analysis scan, and a dynamic scan … all from the command prompt. Let's get started!
Exploring extensions of dependency confusion attacks via npm package aliasing
Dependency confusion attacks are a form of open source supply chain security attacks in which an attacker exploits how package managers install dependencies. In a prior post, we explored how to detect and prevent dependency confusion attacks on npm to maintain supply chain security. In this article, we will present an extension of the dependency confusion problem utilizing npm’s package aliasing capabilities.
The Future of Vulnerability Management Programs
According to the National Vulnerability Database (NVD), the number of new security vulnerabilities increases steadily over the past few years. Image source: NVD The consistent rise in the number of security vulnerabilities along with headline-catching exploits like the SolarWind supply chain attack earlier this year has organizations doubling down on vulnerability management programs to ensure that they are not exposed to malicious attacks.
"PlugWalkJoe" indicted for $784K SIM swap cryptocurrency theft
The U.S. Department of Justice charged a British man for his alleged role in stealing $784,000 worth of cryptocurrency using SIM swap attacks. According to the unsealed indictment, Joseph James O’Connor – also known as “PlugWalkJoe” – conspired with others to steal approximately $784,000 worth of cryptocurrency from a Manhattan-based cryptocurrency company.
The Zero-Trust Journey in 5 Phases
For a concept that represents absence, zero trust is absolutely everywhere. Companies that have explored how to embark upon zero-trust projects encounter daunting challenges and lose sight of the outcomes a zero-trust approach intends to achieve. Effective zero-trust projects aim to replace implicit trust with explicit, continuously adaptive trust across users, devices, networks, applications, and data to increase confidence across the business.
Expanded Suricata detections with Dtection.io
One of the most common questions that Corelight customers and prospects who are using our Suricata integration ask is “what signatures should I run?” While our answer has always started with the industry-standard Emerging Threats Pro feed, we recognize that other feeds - like the ones from Crowdstrike or private industry groups - often make excellent additions to the ET Pro set.
What's new in UpGuard // October 2021 // Cyber Security Product Releases
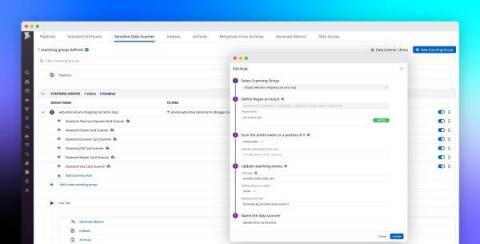
Build a modern data compliance strategy with Datadog's Sensitive Data Scanner
Within distributed applications, data moves across many loosely connected endpoints, microservices, and teams, making it difficult to know when services are storing—or inadvertently leaking—sensitive data. This is especially true for governance, risk management, and compliance (GRC) or other security teams working for enterprises in highly regulated industries, such as healthcare, banking, insurance, and financial services.