The Silent Killer in Security Stacks: Configuration Drift | Todd Graham x Garrett Hamilton
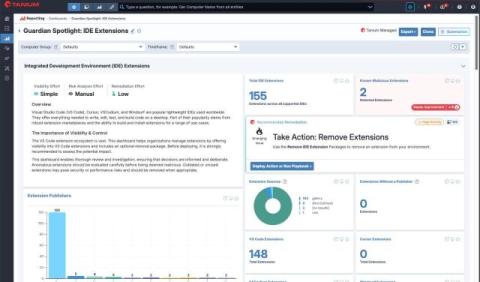
The silent killer in modern security programs? Garrett Hamilton and Todd Graham discuss how the real killer is settings quietly slipping out of alignment over time — even in environments packed with “best-in-class” tools and clean audit results. Misconfigurations don’t announce themselves. They accumulate. They age. They slowly pull your security posture away from original intent. What teams think is “turned on” often isn’t enforced consistently — or at all. Without continuous validation, drift becomes invisible risk.