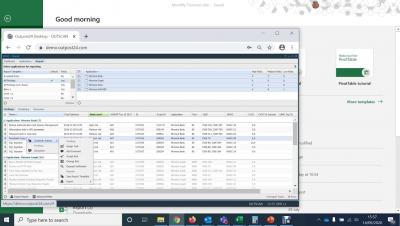
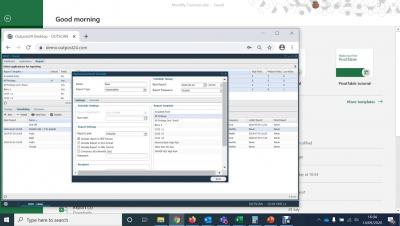
Web Application Security Testing Tools - SWAT Findings
The Secure Web Application Tactics (SWAT) by Outpost24 offers customers a combination of state-of-the-art scanning tools and security experts to provide the most accurate and reliable web application scanning solution available in the market. SWAT does not interfere with daily operations and delivers results with zero false-positives.