Create and Run an Unauthenticated Dynamic Analysis
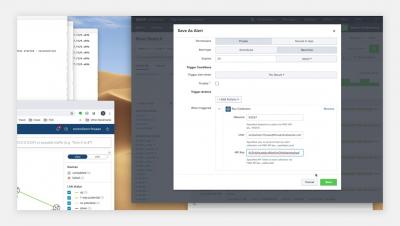
In this video, you will learn how to create, configure, and schedule an unauthenticated Dynamic Analysis. An unauthenticated Dynamic Analysis scan is appropriate when the site you are scanning does not require a login. Veracode Dynamic Analysis also supports the scanning of websites that require authentication, such as such as login via a webform, browser based, or NTLM.