The Open-Source Backdoor That Almost Compromised SSH
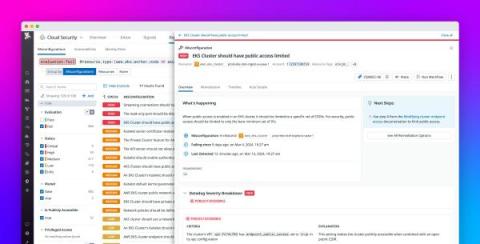
The open-source world narrowly escaped a sophisticated supply-chain attack that could have compromised countless systems. A stark reminder of the necessity of vigilant monitoring and rigorous vetting within the open-source ecosystem to maintain trust and security.