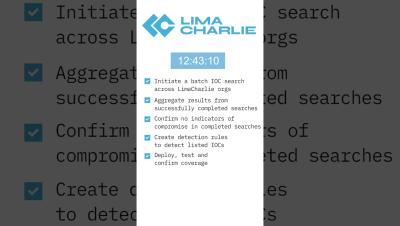
Using SSL Inspection and AI Guardrails to Protect Infrastructure
Using SSL Inspection and AI Guardrails to Protect Infrastructure How do you protect your AI infrastructure from threats without impacting user experience? In this video, we'll cover the methods organizations can use to inspect encrypted traffic, including what is sent to AI chatbots, and add guardrails to protect against security risks. We'll cover.