Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Digital Identity Verification: Paving the Way to a Secure System
As we look forward to restarting our normal lives in the ‘new-normal’ post the pandemic, we are looking to digital channels and devices to bridge the gap between what was done ‘in-person’ and what we can do safely from home. This is necessary for the financial services industry where consumers and businesses alike must move most of their operations online.
10 best practices to build a Java container with Docker
So, you want to build a Java application and run it inside a Docker image? Wouldn’t it be awesome if you knew what best practices to follow when building a Java container with Docker? Let me help you out with this one! In the following cheatsheet, I will provide you with best practices to build a production-grade Java container. In the Java container example, I build using these guidelines, I will focus on creating an optimized secure Java container for your application.
ThreatQuotient Featured on Cisco's ThreatWise TV
Shielding your Kubernetes runtime with image scanning and the Sysdig Admission Controller
Forward Fix: Merged Snapshots
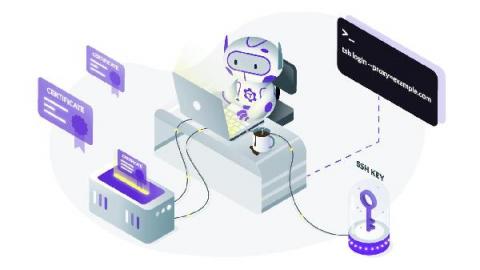
SSH Certificates Security
SSH certificates, when deployed properly, improve security. A half-baked access system using certs is more vulnerable than a public-key-based one if a user or host gets hacked.
Industrial Remote Access: Why It's Not Something to Fear
Increased uptime? Check. Better access to outside expertise? Check. Improved first-time-fix rate? Check. These are just some of the benefits of industrial remote access. Yet many customers are reluctant to embrace remote access. Not only that, but incidents such as the breach at the Oldsmar water utility might increase organizations’ reluctance to use remote access.
ICYM: 4 SaaS Security Lessons to Keep Top of Mind in 2021
At the end of 2020, we hosted a webinar alongside Sisense’s Chief Security & Trust Officer, Ty Sbano titled Securing Best of Breed SaaS applications in 2021. The discussion focused on reviewing the most important security trends of last year and how that should inform security programs this year. As 2021 continues to progress, these are the 4 trends and lessons we think are worth keeping in mind.
CISO Insider S1E6 - CISO Insider Season 1 recap
At Nightfall, we believe in the power of learning from those who have done it before. That’s why we created CISO Insider — a podcast interview series that features CISOs and security executives with a broad set of backgrounds, from hyper-growth startups to established enterprises. Through these interviews, we’ll learn how industry experts overcame obstacles, navigated their infosec careers, and created an impact in their organizations.