Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Customer Corner: RCBC Bank CTO on Balancing Risk and Innovation
Rizal Commercial Banking Corporation (RCBC) begun as a small development bank in the Philippines and has grown to encompass a wide range of financial services and branches in the U.S., Europe, Australia and New Zealand. Like any financial institution, it must comply with a host of regulations and is a prime target for malicious actors.
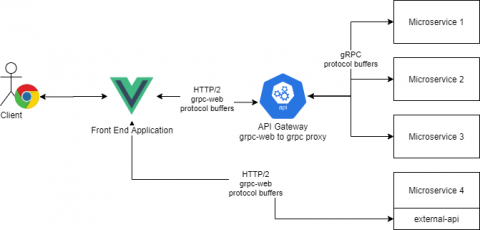
gRPC-web: Using gRPC in Your Front-End Application
At Torq, we use gRPC as our one and only synchronous communication protocol. Microservices communicate with each other using gRPC, our external API is exposed via gRPC and our frontend application (written using VueJS) uses the gRPC protocol to communicate with our backend services. One of the main strengths of gRPC is the community and the language support. Given some proto files, you can generate a server and a client for most programming languages.
Welcome to the Cybersecurity Sessions - Podcast Trailer
Applying Least Privilege in Kubernetes II Jonathan Canada
Adopting Zero Trust and SASE as Fed and SLED Agencies Go Remote-First
The global pandemic further accelerated a trend toward remote work that was already underway, even in federal, state, and local agencies that previously resisted it. But as agencies continue to offer telework options to employees, they must also rethink their security stack to better mitigate the cybersecurity risks that remote work catalyzes. Traditional, perimeter-based approaches to security will no longer work in a cloud-first environment where data can, and is, accessed from just about anywhere.
Don't Warn Your Co-Workers About That Phishing Test
It is October 2021, and another Cybersecurity Awareness Month is upon us. With so much having occurred over the last year, we should all be experts in personal cybersecurity protection. After all, when our homes became our primary business location, it all became very personal. I once worked at a company that prohibited me from offering personal cybersecurity advice.
How secure is your Zendesk instance? Find out with Nightfall's Zendesk DLP scanner
When your customers reach out for help, they send messages to your support team that likely contain personal information. Help desk ticketing systems can often harvest for personally identifiable information (PII) like email addresses and credit card numbers, while healthcare providers using ticketing systems may request protected health information (PHI) like patient names and health insurance claim numbers or phone numbers.
Is Teamviewer safe? Experts & Real Users Answer
You may have previously heard about TeamViewer if you’ve ever needed to remotely access another device for the purposes of maintenance or general work activities.
Why the United States Federal Government Considers Ransomware a Critical Risk to Business
At the Rubrik Data Security Summit, leaders from both the public and private sectors discussed an important topic: ransomware. Cyber threats continue to expand in both volume and sophistication with attacks growing at a rate of 150% annually. As attackers increasingly target backups, it will be even more paramount for policies and guidance from government agencies to match the security innovation of private sector businesses to mitigate the risks of this cyber pandemic head-on.
Active Directory Discovery Detection: Threat Research Release, September 2021
The Splunk threat research team recently developed a new analytic story to help security operations center (SOC) analysts detect adversaries executing discovery and reconnaissance tasks within Active Directory environments. In this blog post, we’ll walk you through this analytic story, demonstrate how we can simulate these attacks using PoshC2 & PurpleSharp to then collect and analyze the resulting telemetry to test our detections.