Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Security Automation Priorities and Challenges: How Do You Compare to Your Peers?
ThreatQuotient’s new survey on the State of Cybersecurity Automation Adoption is now available for download. Conducted by independent research organization, Opinion Matters, the survey includes responses from 250 senior cybersecurity professionals representing the following industries: central government, defense, critical national infrastructure (energy and utilities), retail and financial services.
Utilizing Upbound Crossplane and Styra DAS to Set Policy Across a Modern Technology Stack
1Password
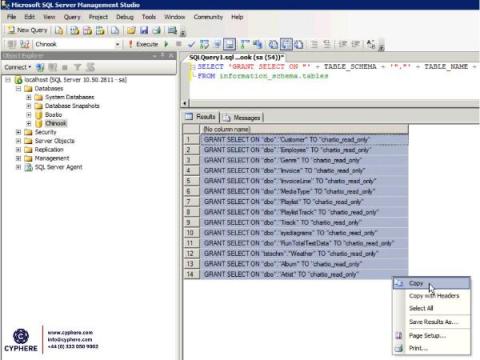
SQL Server Security: Best Practices 2021
In today’s world where digital data is increasing exponentially by the day, the administration and querying of that data are also becoming more and more complex. This huge amount of data is stored in the form of collections within a database. However, in order to create, read, update or delete that data, the database administrators needed the ability to query the database.
Forescout 8.3: What's New
Low-Code SDLC - Build Fast, Stay Secure
Low-code application development provides a solution for a wide range of business needs, from business applications through process automation and integrations. Low-code platforms are becoming a key technology behind the ongoing digital transformation trend, and as such, adoption of low-code platforms is soaring. However, low-code is as much a revolution as it is an exciting new technology.