Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
7 features key to a unified and proactive endpoint security solution
This year’s Cybersecurity Awareness Month has come to an end and, with every passing year, cyberthreats are increasing in number and complexity. Reactive solutions are no longer enough to confront cyberattacks. Organizations must implement proactive strategies to secure their IT assets.
Crossword Cybersecurity Plc Integrates Darkbeam's Cyber Risk Ratings into Rizikon
Titania Launches New Module for Organizations Working with U.S. Government Agencies to Meet Cybersecurity Compliance Accurately
ThreatQuotient Launches ThreatQ v5 to Support the SOC of the Future with Key Data Management Capabilities
Google takes a bold step toward securing your Gmail, but not without many complaints
Many Gmail users were recently greeted with a message that alerted them that 2-step verification will be required to log into their accounts starting on November 9th (today). While many in the security community have been advising people to turn on 2-factor, 2-step, or any other secondary security method on every account as a way to protect the login process, the Twitterverse showed that many people were unhappy with Google’s implementation of this mandatory change.
This Is Arctic Wolf
How Datto made developer-first security a reality with Snyk
When David McCheyne, DevOps Engineer at Datto, outlined a plan to ease the company into developer-first security using Snyk, he thought it would take his teams a year to prove the concept. A seasoned DevOps pro, David understood very well the enormity of this change and was prepared to slowly introduce Datto security champions to the Snyk platform and not force the process.
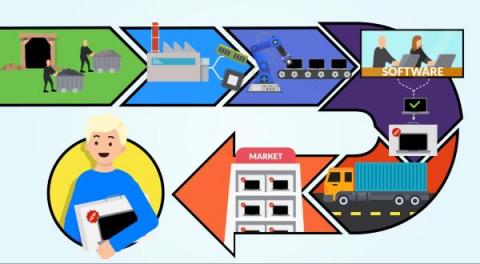
Secure software supply chain: why every link matters
The new threats in software development are not only related to the specific company itself. The whole software supply chain is a target for attackers and it is really important to make sure that we put all our effort into securing each link because if one fails, everything will be affected. Supply chain activities include each step of the transformation of raw materials, components, and resources into a completed product, and its delivery to the end customer.
Elevating What a TIP Can Be - The ThreatQ Platform
In a previous blog I reviewed the foundational use case for a TIP, which is threat intelligence management—the practice of aggregating, analyzing, enriching and de-duplicating internal and external threat data in order to understand threats to your environment and share that data with a range of systems and users. However, one of the unique benefits of the ThreatQ Platform and where organizations are deriving additional business value, is that it also allows you to address other use cases.