Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Appknox Webinar: Effective Cloud Security Episode - 1
Working Anywhere With Egnyte: Mobile Guide
In recent weeks, companies and organizations that ordinarily operate in a more “traditional” office environment have had to pivot quickly to flexible and alternative working arrangements. At Egnyte, our goal has always been to help provide safe, secure access to your content no matter where you are, and that goal has become increasingly more important in the current climate.
The Future is Hybrid: Practicing Security in the Hybrid Cloud
By now, many organizations have adopted the cloud in some way. We saw organizations moving whole servers over to the cloud at the beginning, but now we see small parts of a system being moved to the cloud and new cloud native offerings. We’ll use the analogies of Lincoln Logs and Legos to describe these deployment models.
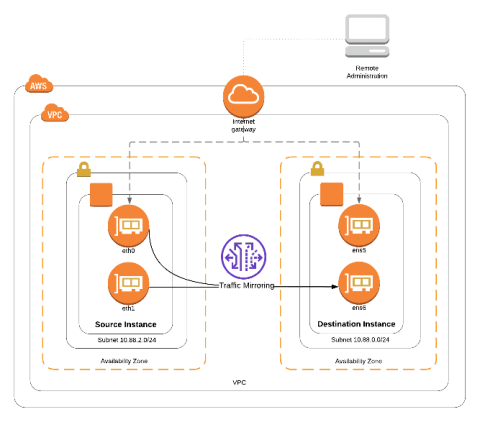
What COVID-19 teaches us about Micro-segmentation and Run-time Cloud Workload Protection
March 2020, the Coronavirus is pretty much everywhere. As I am writing these lines, the number of cases worldwide is 341,334 and 192 different countries have experienced infections.The world is fighting this epidemic and travel limitations are widely used in order to control the spread of the disease. While some say these restrictions are critical, others claim it to be ineffective and redundant. I am not an epidemiologist and will leave that analysis to the experts.