Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The Dual Impact of AI on Power Grids: Efficiency and Vulnerability
Artificial intelligence (AI) has emerged as a promising solution to modernize power grids. The technology, alongside other upgrades like Internet of Things (IoT) connectivity, could make energy infrastructure more reliable and sustainable. However, AI power grids also pose significant cybersecurity risks. Attacks against critical infrastructure are becoming more common. As energy authorities ramp up their investments in AI, they should pay attention to these risks to enable a safer tech transformation.
How Can Deliberately Flawed APIs Help In Mastering API Security?
In our recent webinar recent webinar title 'A CISO’s Checklist for Securing APIs and Applications', we delved into the concept of creating an API security playground tailored for both developer and security teams. The core idea revolves around utilizing intentionally vulnerable APIs as training tools. In this blog post, we'll present a curated list of such APIs, each with its own unique set of characteristics.
JumpCloud's Perspective on July's Global IT Outage
When we look back–in six months, 12 months, or even several years–at the global IT outage that severely disrupted major industries around the world, I don’t think that it will be hyperbole to say that July’s global outage is a watershed moment for IT. Just as the SolarWinds breach was security’s watershed moment, this will end up being IT’s.
Securing Your Cloud: The Critical Role of Firewalls
With any IT environment, especially the public cloud, security is a top concern and priority. When leveraging the public cloud, one of the most important steps to ensuring a protected environment is recognizing the shared responsibility model, as it delineates the security obligations between the cloud provider and your organization.
Better Security and Performance For Free? Why PostgreSQL is Amazing
Upgrade your PostgreSQL instance to the newest version with confidence! In this benchmarking blog post, we show you the performance improvements you can expect when upgrading from PostgreSQL 13 to 16.
What to Look for in the Best QR Code Maker
QR codes have become an indispensable tool for businesses and individuals alike. They offer a quick and efficient way to share information, promote products, and engage with customers. However, to get the most out of QR codes, it's crucial to use the right QR code maker. In this article, we will guide you on what to look for in the best QR code maker, ensuring you can leverage this technology effectively.
Smartphone Security: Tips to Keep Your Data Safe
In today's digital age, smartphones have become an essential part of our daily lives, storing everything from personal contacts to sensitive financial information. With the increasing reliance on these devices, it is crucial to ensure that your data remains secure. This article will provide valuable tips on how to keep your smartphone and its data safe from potential threats.
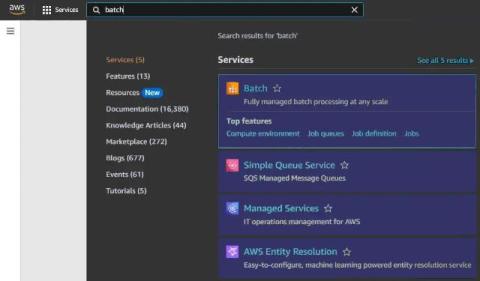
Compute Environments in AWS Batch: How to Set Up
When you need to run training models and complex analysis with batch jobs at scale, AWS batching can be a good solution. AWS provides a special service to perform a large number of computing operations effectively and without management overhead. This blog post covers the AWS Batch architecture and configuration principles for batch processing.
Is ChatGPT Safe?
Depending on how you use it, ChatGPT can be safe. However, to protect yourself and your data, you should be aware of some security risks. These risks include concerns over privacy, shared data with third-party sources, copycat ChatGPT websites and apps and the tool’s tendency to generate misinformation.