Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Agent-Based AI and the Machine Identity Revolution Are Reshaping Security
Is agentic AI the productivity revolution we've been waiting for, or a security nightmare in the making? With AI agents now outnumbering humans and secrets proliferating across enterprise systems, the answer isn't simple. Read our insights from SecDays {France} 2025.
Scaling Without Losing the Human Touch: Delivering AI Customer Service at Enterprise Volume
AI has become the default answer to rising ticket volumes. It's fast, tireless, and cheaper than adding headcount. But somewhere along the way - usually when support crosses into the tens of thousands of interactions a month - teams start hearing the same thing: "It feels like I'm talking to a script." Speed goes up, but the warmth fades.
Ensuring Longevity: The Essential Guide to Epson Printer Ink Management
Maintaining your Epson printer is essential for ensuring optimum performance and longevity. One of the key aspects of printer maintenance is managing yourEpson printer ink efficiently. This involves more than simply replacing cartridges when they run low. A proactive approach to ink management can save costs, reduce waste, and extend the life of your printer. In this guide, we will explore several strategies to manage your Epson printer ink effectively.
See Falcon for XIoT in Action
See how CrowdStrike Falcon for XIoT delivers real-time visibility, AI-powered risk prioritization with ExPRT.AI, and safe protection for connected assets across industrial, IoT, and OT environments. This demo shows how Falcon discovers hard-to-reach XIoT assets in minutes, re-scores vulnerabilities with real attacker context, and helps you focus on what matters most, all while maintaining operational continuity.
API Iceberg: The Hidden Risk Lurking Below the Surface #APIsecurity #InternalAPIs #HiddenRisk
Most security teams focus on public APIs—but what about the internal ones you can’t see? As architectures evolve, hidden APIs become silent threats.
What is a Cloud-Native Security Automation Framework? Benefits & Use Cases
We live in a world where infrastructures reside entirely in the cloud, threats evolve faster than ever, and attackers never sleep. Manual security processes simply can’t keep pace. Cloud-native security automation is the critical solution for organizations to secure large attack surfaces.
What CISA's BOD 25-01 Means for API Security and How Wallarm Can Help
The US government has taken another significant step towards strengthening cloud security with the release of CISA’s Binding Operational Directive (BOD) 25-01. Aimed at improving the security posture of federal cloud environments, BOD 25-01 mandates robust configuration, visibility, and control across cloud-based services. While the directive doesn’t explicitly name API security, securing modern cloud systems relies on securing APIs - including the ones security teams don’t know about.
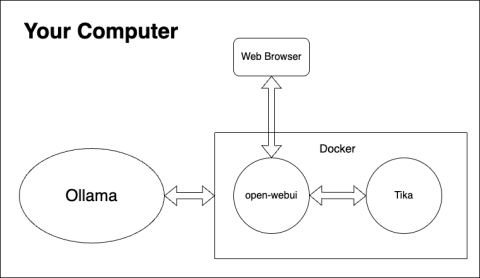
Empowering your LLMs: Unlocking cybersecurity queries with Open WebUI knowledge bases
In the rapidly evolving landscape of large language models (LLMs), the ability to access and synthesize vast amounts of information is paramount. While LLMs excel at generating creative text and understanding complex prompts, their knowledge is often limited to the data used during their training. This is where knowledge bases (a.k.a.
The quantum-AI collision: What CISOs must do now to stay ahead
Technology is moving at the speed of light, and two forces—quantum computing and AI agents—are poised to shake up cybersecurity. We’re not talking about some far-off future; this is happening now. The message for CISOs and security leaders is simple: If you’re not preparing now, you’re already behind. As we say in Brazil, “Melhor prevenir do que remediar” or “better to prevent than remediate.”