Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Detectify announces new product names
STOCKHOLM, SWEDEN – Detectify, the SaaS security company powered by ethical hackers, announces new product names for the core products developed for security teams defending medium to large enterprise companies. On November 11th, the product names will be switched from Asset Monitoring to Surface Monitoring, and where you previously saw Deep Scan you will now see Application Scanning.
How Snyk Code prioritizes vulnerabilities using their Priority Score
If every vulnerability seems to be equally critical, engineers would get overwhelmed and probably waste time on the wrong issues. This is why it’s important for developer security tools to provide clear and simple prioritization functionality. As you’ve likely noticed, Snyk Code provides a Priority Score on the top right corner of the overview panel. When hovering over it, an explanation is shown how the priority score was calculated.
Understanding The 2021 Gartner Market Guide for Managed Detection and Response Services
How to effectively detect and mitigate Trojan Source attacks in JavaScript codebases with ESLint
On November 1st, 2021, a public disclosure of a paper titled Trojan Source: Invisible Vulnerabilities described how malicious actors may employ unicode-based bidirectional control characters to slip malicious source code into an otherwise benign codebase. This attack relies on reviewers confusing the obfuscated malicious source code with comments.
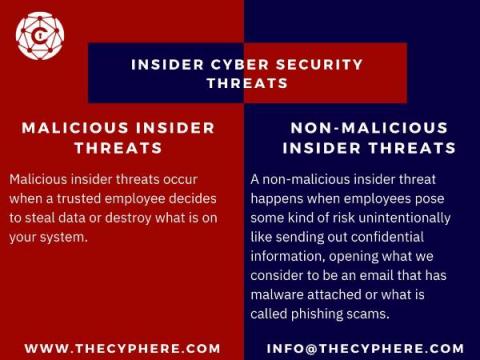
What is a Cyber Threat? Types and Sources
A cyber threat is any kind of attack against what we consider cyber security. Cyber security is what we use to protect our computers and networks from intrusions or attacks that can be harmful to us. There are many different types of cyber threats like malware, ransomware, botnets and phishing scams etc.
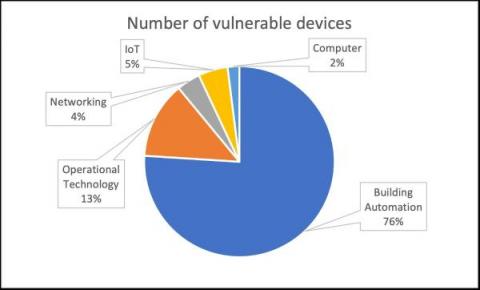
New Critical Vulnerabilities Found on Nucleus TCP/IP Stack
Forescout Research Labs, with support from Medigate Labs, have discovered a set of 13 new vulnerabilities affecting the Nucleus TCP/IP stack, which we are collectively calling NUCLEUS:13. The new vulnerabilities allow for remote code execution, denial of service, and information leak. Nucleus is used in safety-critical devices, such as anesthesia machines, patient monitors and others in healthcare.
Vendor Management Best Practices
Establishing positive vendor relationships is crucial to running a successful business. Nonetheless, vendor management has several moving parts, and you have a lot of things to keep track of. This includes who your third parties are, the services they offer, which internal policies apply to them, and what sensitive data they have access to. Without a strong foundation of vendor management best practices, vendor risks could manifest into failures that could affect business continuity.