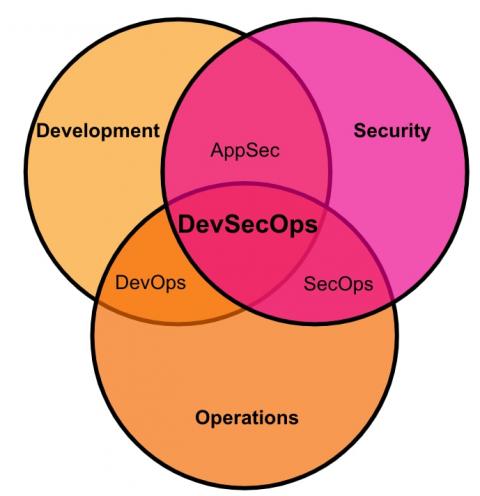
Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Panel Discussion // UpGuard Summit November 2022
DevSecOps: The What, Why, Who, and How
By way of a brief introduction, I have had a 25+ year career in technology, and this has come with some wonderful experiences and opportunities along the way. One constant throughout my journey has been a need to increasingly leverage data, enabling informed decisions (even automated) at all levels to ensure: secure, high performing and observable products and services are available to the customers and partners I’ve been supporting.
How Did the Cash App Data Breach Happen?
The CashApp data breach was caused by a former employee who accessed customer financial reports as an act of revenge against the company after their employment was terminated. According to the April 2, 2022 filing with the Securities Exchange Commission by Block (CashApp’s parent company), the employee required access to the financial reports as part of their daily duties.
How to Become HIPAA Compliant in 2022 (Includes Checklist)
HIPAA compliance is regulated by the Department of Health and Human Services (HHS) and enforced by the Office for Civil Rights (OCR). In 2013, the final Omnibus rule was enacted, binding business associates - or third-party vendors - to the Health Insurance Portability and Accountability Act. This modification added another level of compliance complexity to an industry not accustomed to operating in the cybersecurity domain - the healthcare industry.
5 Tips for Linux Server Hardening
Active Directory Security
At its core, Active Directory domain services (AD DS) is a structured data store of objects in the domain controller. It is a directory service from Microsoft for identity management and access control in Windows domain networks. Active Directory can authenticate users, groups, services and computers to protected information. In addition to that, AD DS also helps to implement security policies and permissions. AD DS enforces them for all computers in your network.
9 Steps to Mitigate Ransomware Attacks for Your Business
Ransomware attacks have become so prevalent in recent years that it’s no longer a matter of “if” your business may be the victim of a ransomware attack, but “when.” In fact, in 2021, 37% of global organizations reported that they were the victim of a ransomware attack. To mitigate the impact and probability of ransomware on your business, you must continuously look for new ways to secure your network and maintain continuous cybersecurity monitoring.