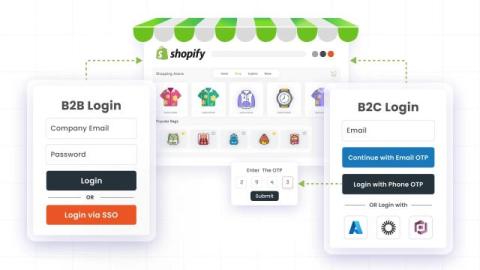
How to Implement Separate B2B and B2C Login & Onboarding in Shopify
Shopify stores are evolving beyond simple retail operations. What once was a primarily consumer-focused platform is now powering complex B2B experiences with tiered pricing, customer groups, and negotiated catalogs catering multiple B2B vendors and companies. However, as stores diversify their audiences, authentication becomes a critical pain point. A login flow designed for retail customers might be fast and convenient.