Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Zero Trust
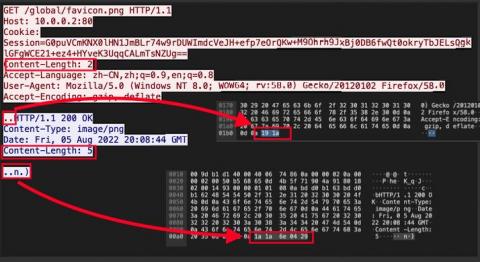
Detecting the Manjusaka C2 framework
Security practitioners may know about common command-and-control (C2) frameworks, such as Cobalt Strike and Sliver, but fewer have likely heard of the so-called Chinese sibling framework “Manjusaka” (described by Talos in an excellent writeup). Like other C2 frameworks, we studied the Manjusaka implant/server network communications in our lab environment, and here we document some of the detection methods available. We have also open-sourced the content we describe.
Why You Should Avoid Public WiFi
The ability of a cybercriminal to place themselves between you and the connection point poses the biggest security vulnerability to public WiFi. You unknowingly communicate with the cybercriminal, who then collects and passes your information to the hotspot, rather than you connecting to the hotspot directly. While there are ways to stay protected on public WiFi, it is still advisable to avoid using it.
IT admin admits sabotaging ex-employer's network in bid for higher salary
A 40-year-old man could face up to 10 years in prison, after admitting in a US District Court to sabotaging his former employer’s computer systems. Casey K Umetsu, of Honolulu, Hawaii, has pleaded guilty to charges that he deliberately misdirected a financial company’s email traffic and prevented customers from reaching its website in a failed attempt to convince the firm to rehire him at a greater salary.
Forward Networks Named a Global Leader in Cloud Computing for the Second Time
Cloud Insecurities - How to threat hunt in hybrid and multi cloud environments
[Demo Video] Corelight + CrowdStrike Falcon XDR
CVE-2022-3236 - Remote Code Execution Vulnerability in Sophos Firewall
FBI Notice Underscores Cyberthreats Posed by Medical Devices and IoMT - Risk Management Can Help
On September 12, the FBI released a private industry notification entitled “Unpatched and Outdated Medical Devices Provide Cyber Attack Opportunities.” The notification underscores how a growing number of vulnerabilities in medical devices and Internet of Medical Things (IoMT) assets can be exploited by threat actors to “impact healthcare facilities’ operational functions, patient safety, data confidentiality and data integrity.”