Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Vulnerability
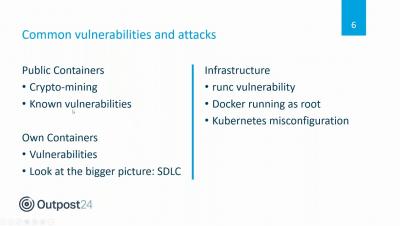
New Vulnerability Exposes Kubernetes to Man-in-the-Middle Attacks: How to Mitigate CVE-2020-8554
A few weeks ago a solution engineer discovered a critical flaw in Kubernetes architecture and design, and announced that a “security issue was discovered with Kubernetes affecting multi-tenant clusters. If a potential attacker can already create or edit services and pods, then they may be able to intercept traffic from other pods (or nodes) in the cluster.” If a hostile user can create a ClusterIP service and set the spec.externalIP field, they can intercept traffic to that IP.
How attackers exploit the WordPress Easy-WP-SMTP zero-day
On November 6th, 2019, Detectify added security tests for 50+ of the most popular WordPress plugins, including Easy-WP-SMTP. Although the zero-day affecting Easy-WP-SMTP (CVE-2020-35234) was recently patched, WordPress estimates that many of the 500,000+ active installs of the plugin remain unpatched. Detectify scans your applications for this vulnerability and alerts you if you are running a vulnerable version of WordPress and WordPress plugins.
Continue Clean-up of Compromised SolarWinds Software
Last week, the United States Cybersecurity & Infrastructure Security Agency (CISA) advised on initial steps to take in response to the SolarWinds software that was compromised by advanced persistent threat actors. While federal agencies were under a deadline to complete certain actions, this issue will require continued clean-up and longer-term efforts to mitigate the threat.
Top 10 Open Source Vulnerabilities In 2020
If 2020 taught us anything, it’s to expect the unexpected. While there don’t seem to be enough words to cover the changes that we all did our best to adjust to, we are more than happy to give you our rundown of the top 10 open source vulnerabilities in 2020.
CyRC analysis: Authentication bypass vulnerability in Bouncy Castle
CVE-2020-28052 is an authentication bypass vulnerability discovered in Bouncy Castle’s OpenBSDBcrypt class. It allows attackers to bypass password checks.
Contact Form 7 (5.3.1 & below) Vulnerable To Unrestricted File Upload
State of Software Security v11: The Most Common Security Flaws in Apps
For our annual State of Software Security report, we always look at the most common types of security flaws found in applications. It’s important to look at the various types of flaws present in applications so that application security (AppSec) teams can make decisions about how to address and fix flaws. For example, high-severity flaws, like those listed in OWASP Top 10 or SANS 25, or highly prevalent flaws can be detrimental to an application.
Fix now: Vulnerabilities targeting the FireEye Breach
On Tuesday 8th December in an unprecedented move leading cybersecurity provider FireEye admitted they had been breached and several of their red team tools and scripts had been stolen. In this blog we look at the list of vulnerabilities in these tools and how to protect your organization.