Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
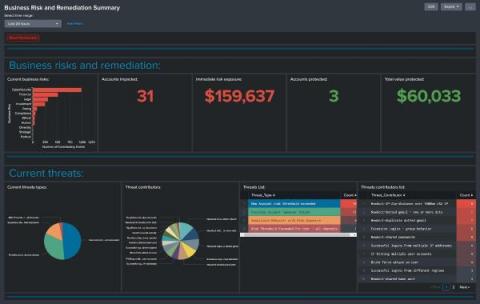
Detect Fraud Sooner with the Splunk App for Fraud Analytics
It will not come as a surprise to you that fraud and financial crime is continuing to challenge organizational business and cyber resiliency plans. Odds are you have dealt with fraud firsthand, or know someone experiencing the pains caused by fraud. Back in 2020 we shared some thoughts about how we believe leveraging a data platform like Splunk can help you gain more anti-fraud value and insights from your data and showed how you can determine what your data is worth.
Covered Entities vs Non-Covered Entities Under HIPAA
The Health Insurance Portability and Accountability Act (HIPAA) was enacted in 1996 and sets forth a comprehensive set of standards for protecting sensitive patient health information. The Privacy Rule applies to all entities that fall within the definition of a “covered entity“, which generally includes healthcare providers, health plans, and clearinghouses.
What DNS over HTTPS (DoH) Is & How to Enable in Windows 10
When your web browser accesses a website, it needs to first translate the friendly URL (such as Netwrix.com) to the public server IP address of the server that hosts that website. This is known as a DNS lookup. Traditional DNS is unencrypted, unlike modern HTTPS web traffic that’s almost entirely secured via HTTPS these days.
Evolving Threats in the Cloud and What They Mean
Innovate with AWS and Secure with CrowdStrike
Women In Cyber Security | Razorwire Podcast
60 Second Charity Challenge: Cybersecurity Awareness Month
Unifying Construction Documents with Procore and Egnyte
It is not uncommon on the job site to find project teams using a variety of disparate applications to access, share and collaborate on documents - each with their own storage, permissions and controls. This makes it very challenging to manage that project information, as it flows in and out of teams, and across different software platforms.
Top Collaboration Challenges In Clinical Trial Outsourcing
For biotech organizations, collaboration is the lifeblood of clinical research. A typical clinical trial depends upon constant communication, data sharing, and myriad other interactions among sponsors, sites, CROs, and participants. A breakdown in collaboration can cause delays that threaten the entire operation.