Secure Enterprise AI Apps and Agents: Visibility, Governance, Runtime Protection
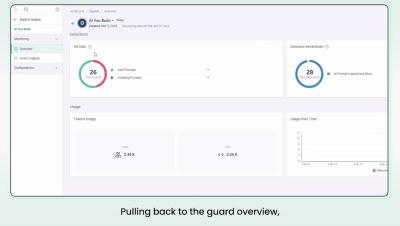
When you deploy an AI application, do you know what's being sent into it — or what's coming back out? Cato AI Security provides runtime protection for the AI applications your organization builds and deploys, with real-time enforcement, sensitive data anonymization, and a complete audit trail across every interaction.