Controversy and Criticism: Navigating Resistance to Cyber Risk Clarification | Razorthorn Security
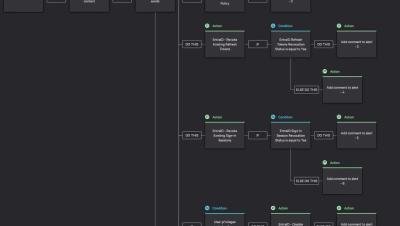
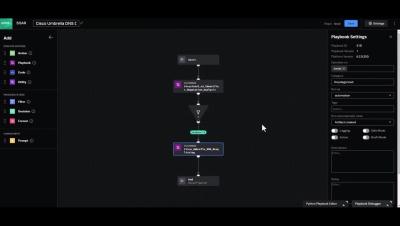
Dive into the contentious realm of cyber risk clarification in this eye-opening video. Explore the challenges faced by proponents of risk assessment methodologies as they encounter resistance from influential figures in the industry. Hear about the shocking experiences of individuals who have been met with accusations of criminal negligence simply to advocate for clearer risk communication. Despite the pushback, join us as we navigate through the discourse and strive to shed light on the importance of cyber risk understanding and mitigation.