Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Francis Odum Talks to Torq about the Modern SOC
The future of SOC automation is dynamic and rapidly evolving, promising to revolutionize how security operations centers (SOCs) tackle their most pressing challenges. As cybersecurity threats grow in volume and sophistication, SOC teams are increasingly overwhelmed by alert fatigue, false positives, and a critical shortage of skilled professionals.
Reducing Storage Spend: The CISOs Guide to Efficient and Effective Security Operations
As data volumes grow exponentially, CISOs face the mounting challenge of managing storage costs without compromising security. Storing vast amounts of security data can quickly become cost-prohibitive, and inefficient storage solutions can lead to budget overruns. This webinar will explore how LimaCharlie can help reduce storage spend while maintaining robust security measures.
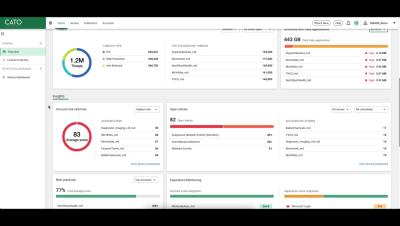
MSASE Dashboard Overview
Managing multiple customers from a single console is good, but being able to get all of the analytics and usage data all in a single dashboard is amazing. Cato’s MSASE Partner Platform Dashboard provides just that...a single pane of glass to see all of your customer account analytics, with actionable data and deep-linking to the customer tenants.
Simplifying FedRAMP Compliance with Teleport
FedRAMP compliance is notoriously challenging, but it doesn't have to derail your DevOps flow or tech stack. Discover how Teleport’s robust infrastructure access and security platform addresses some of the toughest questions and hurdles in the FedRAMP process, empowering engineering, compliance, and security leaders to implement and enforce security controls seamlessly.
Building a Human-Centric Vulnerability Management Program
Steve Carter, CEO and co-founder of Nucleus Security, and Dr. Nikki Robinson, Security Architect at IBM, discuss the importance of the people side of vulnerability management. They explore challenges such as context switching, long mean time to remediation, and the impact of communication on vulnerability management programs. The conversation includes practical advice on incorporating human factors into cybersecurity practices, how to improve communication and collaboration among teams, and why understanding human factors is crucial for effective vulnerability management.
Demo Tuesday | Special Cisco Live Edition | Full Demo
If you've ever wished Demo Tuesdays were longer OR if you've always wondered what Mike looks like in sequins-- this is the stream you've been waiting for. Mike takes our Cisco Live Demo Theater audience through a full 30 minutes of Forward Enterprise product demonstration live in Las Vegas.
Configuring RADIUS | JumpCloud University Tutorial (2024)
In this tutorial, you'll see how to configure JumpCloud's Cloud RADIUS for your organization, Wireless or VPN networks. JumpCloud's Cloud RADIUS allows you to use either JumpCloud or Azure AD as your identity provider. Cloud RADIUS also supports Certificate Based Authentication, allowing you to bring your own certificates for Passwordless authentication. To discover more resources checkout JumpCloud University where you’ll find courses, tutorial videos, engaging guided simulations, and end user content.
Veracode's Application Risk Management Platform
Build and scale secure software from code to cloud with speed and trust. Veracode’s Platform allows you to start fast and scale, enable real-time flaw remediation, and gain actionable visibility into your application risk.
Cyber Alert III | The Last Stop | WatchGuard Technologies
In the latest episode of The Last Stop, watch how the Seattle Kraken IT team effortlessly defends against cyber alerts with WatchGuard. Join Philipp Grubauer and the team as they demonstrate top-notch cybersecurity strategies, proving they are The Last Stop of Defense.