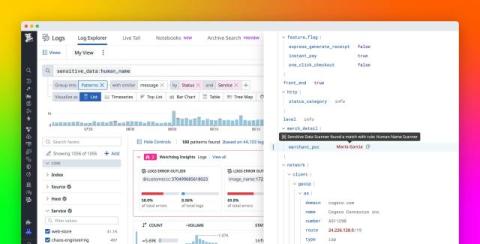
Detect human names in logs with ML in Sensitive Data Scanner
Modern applications generate a constant stream of logs, some of which carry more information than they should. For too many organizations, logs include personally identifiable information (PII) such as customer names that were never meant to leave production systems. Teams try to limit this data exposure by using regular expressions to detect and obfuscate matches, only to discover that names like John O’Connor, Mary-Jane, Jane van der Meer, and A. García slip through.