Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Deep Web vs Dark Web: What's the Difference?
The main difference between the deep web and the dark web is that the deep web is bigger and used every day by most people without even realizing it. The dark web can only be accessed with the Tor browser and is riskier to access than the deep web. Continue reading to learn more about the differences between the deep and dark web, and how you can keep your information protected from both.
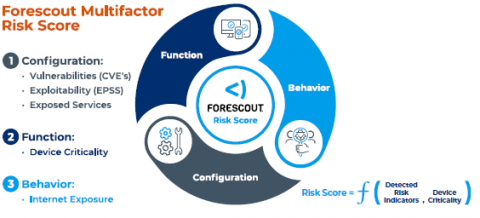
Go Beyond Device Visibility to Prioritize and Act on Cybersecurity Risk
When I joined Forescout as CEO six months ago, I was excited to partner with our strong employees, management team and board as we take the company through its next phase of growth. Today I’m pleased to announce enhancements to the Forescout® Platform that will help customers fully understand the risk posture of their attack surface and enable their security teams to focus on remediating the assets that pose the most risk.
Using insecure npm package manager defaults to steal your macOS keyboard shortcuts
Malicious npm packages and their dangers have been a frequent topic of discussion — whether it’s hundreds of command-and-control Cobalt Strike malware packages, typosquatting, or general malware published to the npm registry (including PyPI and others). To help developers and maintainers defend against these security risks, Snyk published a guide to npm security best practices.
Free CCPA Vendor Questionnaire Template (2023 Edition)
SecurityScorecard and the U.S. Chamber of Commerce
This week, SecurityScorecard is participating in the US Chamber of Commerce’s Cyber Security Trade Mission to Israel. This has been a valuable experience to not only share our cybersecurity knowledge, but to learn more about Israel’s cybersecurity efforts, and those of other countries.
Five Tips for Using SBOMs to Boost Supply Chain Security
A Software Bill of Materials (SBOM) is a key cyber defense item — it identifies what’s in your software, applications, and code base so that you can detect and mitigate risk more effectively. This is useful when it comes to application security because companies can only detect and fix vulnerabilities if they know what’s there in the first place. SBOMs give you that visibility. Consequently, SBOMs are now a “must-have” tool for most companies.
Threat Detection In 2023 Is Broken. Here's How to Fix It
Why have cyber incidents topped the Allianz Risk Barometer for the last two years in a row? Growing attack surfaces are partly responsible. Remote work, cloud migration, IoT use and other trends give cyber threats more places to enter and hide within networks. But there is another cause – deficiencies in the standard approach to threat detection and response.