Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
A CISO's perspective: Why I've read the Elastic Global Threat Report
Getting started with query parameterization
When web applications rely on user-supplied data, there is a potential risk of SQL injection attacks. SQL injection is a technique used to alter a SQL statement by manipulating user input. Specifically, attackers send malicious SQL code to the database to bypass security measures and gain unauthorized access to data. The consequences can be severe, ranging from sensitive information leaks to complete system loss.
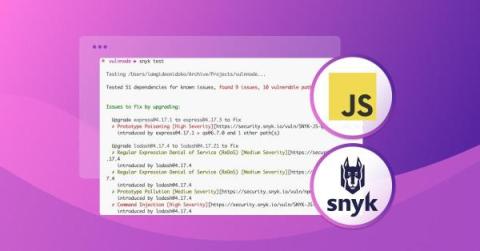
How to secure JavaScript applications right from the CLI
According to Snyk's 2022 State of Open Source Security report, the average JavaScript project has 49 vulnerabilities, including common ones like unsafe dependencies, cross-site scripting (XSS), weak input validation, and cross-site request forgery (CSRF). And given JavaScript's widespread use, robust security measures are increasingly important to safeguard your applications from cyberattacks.
Streamline Document Structure and Access Control with Egnyte and Microsoft Teams Integration
As the world of remote work and digital collaboration continues to evolve, the need for efficient file management and secure access control is becoming increasingly critical. To address this, Egnyte has rolled out additional improvements to its integration with Microsoft Teams that are aimed at simplifying permission management, improving document organization, and enhancing collaboration processes. Automated MS Teams and Channels mapped to the Egnyte Folder.
5 Tripwire Enterprise Misconfigurations to Avoid
Configuration management is vitally important as part of a sound cybersecurity strategy. We have previously published how patching alone is not enough, as that does not alter a system’s customized configuration. Misconfigurations can be as damaging to security as a deliberate attack on a system.
The growth of APIs attracts Cybercrime: How to prepare against cyber attacks
Application Programming Interfaces (APIs) have profoundly transformed the internet's fabric. In the pre-API era, digital interactions were limited by siloed systems functioning in isolation. APIs dismantled these barriers by introducing a universal language that diverse applications could comprehend. This linguistic bridge facilitated an unprecedented level of interconnectivity between software entities.
Oh-Auth - Abusing OAuth to take over millions of accounts
SIAM - bringing a layer of clarity to complex environments and vendor ecosystems
Today’s modern IT environment is complex and challenging for organisations to navigate. Not only has the threat landscape evolved, but we are seeing more compliance and regulation as well as ongoing economic pressures. This is all putting additional strain on already resource-stretched internal IT teams.
How to Spot a Next-Gen SIEM Imposter
Staying ahead of the cybersecurity curve can feel like running a marathon uphill, and the right SIEM is key to leveling the playing field. Smarter SIEM solutions have emerged from the cloud to address the changing demands of today’s security operations. Unlike legacy SIEMs, which were designed for on-premises deployments and have limited scalability, more innovative next-gen solutions offer cloud-native SaaS models that provide greater flexibility and scalability.