Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
How to Hide Products Based on Customer Tags in Shopify
As Shopify stores scale, product visibility needs to be more controlled; merchants handling different customer types often prefer not to expose products to everyone. Whether you’re managing B2B catalogs or exclusive offerings, the ability to restrict products by customer tags in Shopify becomes essential. While customer tags are useful for categorization, Shopify doesn’t provide built-in functionality to link those tags with product visibility.
A better way to protect data stored on Synology NAS
For many businesses and MSPs, Synology is not just “a NAS box.” It is where shared files live, branch office data accumulates, backups land and teams expect fast local access to critical information. Synology itself positions its portfolio squarely around NAS and data protection for business use, and its Package Center supports both Synology-developed and third-party applications.
Data Sovereignty and Cross-Border Backup Compliance
When organizations think about regulatory compliance, they typically focus on where production data lives. What they often miss is that every backup copy, every replicated snapshot, and every disaster recovery failover target carries the same legal weight as the original data. As governments tighten data sovereignty laws across the EU, APAC, and beyond, backup and disaster recovery infrastructure has become a compliance minefield — and most IT teams don't know they're standing in it.
Rubrik SAGE: Semantic Agent Control That Scales for the Enterprise
Are you ready to take control of your AI agents with Rubrik Agent Cloud? Traditional keyword filters aren't enough when agents are acting autonomously. You need a true AI governance engine to manage them effectively! SAGE is our semantic AI governance engine that allows you to define custom policies using natural language and block risky tools in real time. Ready to secure your autonomous agents? Dive into SAGE and learn more by checking out our website.
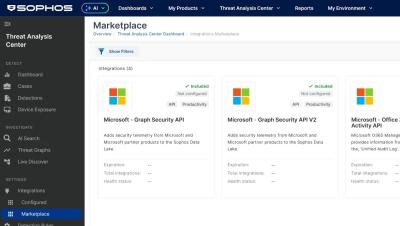
Microsoft + Sophos: The MSP Profitability Advantage
Sophos enhances the Microsoft environments your customers already trust — helping you deliver stronger outcomes, clearer value, and a more defensible service offering. If you’re ready to build a more profitable and scalable Microsoft security practice, let’s talk.
NVIDIA Just Made AI Agents Production-Ready #ai #shorts
AI agents just became production-ready overnight. With NVIDIA’s new NeMo Guardrails / NemoClaw-style agent control systems, AI agents can now operate in controlled environments with policies, sandboxing, and guardrails. Sounds safe… but there’s a catch. Agent safety protects what the AI does. But it doesn’t secure what the AI knows. And that’s where the real enterprise risk appears. In this video we break down the difference between.
Smishing AI
Cybercriminals are evolving—and so are their tactics. Smishing, or SMS phishing, has become one of the fastest-growing mobile threats. With AI, attackers can now create convincing, personalized messages in seconds—removing language barriers and making scams harder than ever to detect. That’s where Lookout Smishing AI comes in. Our advanced AI-powered detection goes beyond scanning for malicious links. It identifies the intent behind every message—stopping social engineering attacks before they reach you. Whether there’s a URL or not, Lookout keeps your mobile workforce protected.
Mobile Threat Report Briefing
In this video, David Richardson, Product CTO at Lookout, provides a strategic overview of the evolving mobile threat landscape based on Q3 2025 global enterprise data. Key Insights: Dominant Attack Vectors: Mobile phishing and social engineering remain the most significant threat categories. Attackers are increasingly using AI-powered tools to craft authentic-looking messages and conduct deep research for highly targeted attacks.
IRGC threatens tech companies, FBI Director hacked, Venom Stealer & Hasbro breach / Intel Chat [307]
In this episode of The Cybersecurity Defenders Podcast, we discuss some intel being shared in the LimaCharlie community. Support our show by sharing your favorite episodes with a friend, subscribe, give us a rating or leave a comment on your podcast platform. This podcast is brought to you by LimaCharlie, maker of the SecOps Cloud Platform, infrastructure for SecOps where everything is built API first. Scale with confidence as your business grows.
Stopping JSCEAL Before Data Theft Begins: Detection and Prevention in Cato SASE
JavaScript-based crypto stealers are designed to hide in plain sight. They arrive over innocent-looking, encrypted web traffic and aim to steal credentials and wallet data before anyone notices. In this demo, you’ll see how the Cato SASE Platform stops a real JavaScript crypto stealer (JSCEAL) in real time. We show: How the malware is delivered over standard web traffic How Cato inspects encrypted traffic inline, in a single pass How the attack is identified and blocked before it reaches the endpoint How security teams get immediate visibility in the Cato Management Application.