Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Cloud Threats Memo: Staggering Statistics About Recent Cloud Misconfigurations
Cloud misconfigurations continue to be a serious concern for organizations, and the list of security incidents caused by the exposure of data from Saas and IaaS applications only continues to grow.
Pull Requests for Infrastructure Access
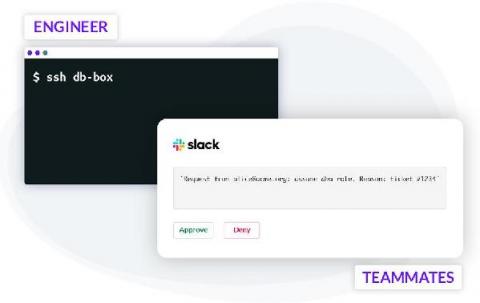
Making frequent changes to cloud applications running in production is the de-facto standard. To minimize errors, engineers use CI/CD automation, techniques like code reviews, green-blue deployments and others. Git pull requests often serve as a foundational component for triggering code reviews, Slack notifications, and subsequent automation such as testing and deployments. This automated process enforces peer reviews and creates enough visibility to minimize human error.
De-Risking Network Automation By Integrating with Itential
Today’s networks are too complex for manual network management and updates. With most enterprises composed of tens of thousands of devices spanning multiple geographical locations, on-premises hardware, Virtual environment, and multiple clouds – it’s virtually impossible to push updates manually. Also – the sheer volume of vendors and coding languages can be overwhelming for a network operations engineer.
Access this computer from the network - best practices for DC and Member Server
Veriato
Device management blind to 125 percent increase in financial sector phishing attacks
As guardians of valuable monetary assets and highly sensitive data, financial institutions are the perfect target for cybercriminals. According to IBM, the financial services sector was the number one target of cyberattacks in 2020 among all industries. This means these organizations continue to be challenged and invest heavily in both people and technology to make sure they can withstand attacks of any type.
NSA offers advice: connecting OT to the rest of the net can lead to "indefensible levels of risk"
The US Defense Department and third-party military contractors are being advised to strengthen the security of their operational technology (OT) in the wake of security breaches, such as the SolarWinds supply chain attack.
Confessions of a Digital Security and Fraud Director
What’s the point of collecting a lot of data if you don’t have the tools and power to analyze it? In this Log’s Honest Truth podcast, presented in partnership with ITSP Magazine, Devo’s VP of Customer Success, Jill Orhun, discusses the confessions of “Mr. V,” a digital security and fraud director. His face and voice are disguised, but there’s no disguising his frustrations. Listen to the podcast. “Mr.
Are bots threatening the travel industry in 2021?
In our recent webinar, Netacea’s Head of Threat Research, Matthew Gracey-McMinn, and Enterprise Sales Manager for Travel and Tourism, Graeme Harvey, were joined by Director of Spike Digital, Duncan Colman, to delve into the top bots and cybersecurity threats set to target the travel industry in 2021.
Splunk SOAR Playbooks: Suspicious Email Domain Enrichment
Despite the myriad pathways to initial access on our networks, phishing remains the single most popular technique for attackers. The open nature of email and our reliance on it for communication make it difficult for defenders to classify messages, so it is no surprise that suspicious email investigation is a top use case for automation. Today, we are releasing a new community playbook for Splunk SOAR (previously Splunk Phantom) to help enrich suspicious email events.