Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
SANS 2021 Cyber Threat Intelligence Survey Report:
Cynet Appoints Nuvias as European Distributor
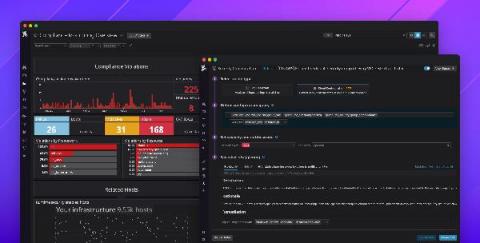
Introducing Datadog Cloud Security Posture Management
Governance, risk, and compliance (GRC) are major inhibitors for organizations moving to the cloud—and for good reason. Cloud environments are complex, and even a single misconfigured security group can result in a serious data breach. In fact, misconfigurations were the leading cause of cloud security breaches in 2020. This puts a lot of pressure on developer and operations teams to properly secure their services and maintain regulatory compliance.
6 Strategies for Cybersecurity Risk Mitigation
This past year saw nearly a 300% increase in reported cybercrimes, according to the FBI’s Internet Crime Complaint Center (IC3). There has been a clear rise in threat volume and sophistication as many cybercriminals shift to techniques that can effectively evade detection and easily go after high-value targets. IoT devices are becoming a focus for threat actors, and threats related to credential harvesting and ransomware are also growing in number.
Back to the office...
As the world is starting to move out of lockdown, businesses are moving some of their workforce back into the office environment. Whilst their focus may be on the logistics of this and making the office environment ‘Covid-Safe’ for their employees, they also need to be cognisant of the potential security challenges facing them.
Yochai Corem, CEO of Cyberint on i24NEWS comments on the REvil/Kaseya ransomware attack
Top 5 high severity CVEs detected by Detectify since June 2020
We’re going to highlight the Top high severity CVEs found by Detectify. Thanks to the Crowdsource global community of handpicked ethical hackers, Detectify users get continuous access to the latest threat findings “from the streets” – even actively exploited vulnerabilities for which there aren’t yet any official vendor patches or updates.
Empower Your Data Governance
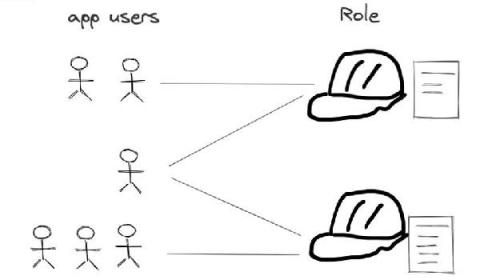
RBAC and ABAC with AWS IAM
This is a guest blog post from Shuo Yang in his blog series “Transitioning to Programming the Cloud”, as a part of our blog posts focusing on Identity, Security and Access. We talked about how AWS CIP, STS and IAM can serve as the foundation of application authorization in our last post, i.e., how the application gets the temporary credential representing a specific role (i.e.
Critical Data Breach Stats for Australian Businesses in 2021
If you're an Australian business reading this, there's a 30% chance you will suffer a data breach. Such cutthroat statistics, as uncomfortable as they are to read, are important to be aware of if you want to avoid becoming one. To help you achieve a data-driven approach to cybersecurity, we've aggregated some of the most critical data breach stats for Australian businesses. This list also includes global data breach statistics that could be a window into Australia's future modified threat landscape.