Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
The Government Cyber Security Strategy
CAPTCHA Risks: More dangerous than useful?
CAPTCHA and reCAPTCHA are an ever-present component on any website that requires user interaction. But the risks of embedding CAPTCHA/reCAPTCHA plugins on a website can outweigh the benefits. Flawed code can increase the threat of client-side attacks. Who hasn’t encountered a CAPTCHA?
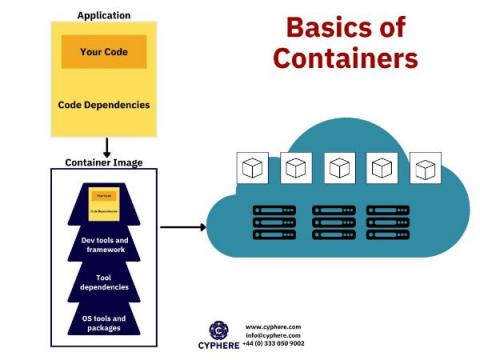
What is Container Security?
A container is defined as packaged software that contains all the code and dependencies of an application within a virtual environment so that the application can be migrated from any computing device to another. Docker container images are executable software packages that are lightweight and standalone.
Wi-Fi Hacking: How to Secure a Wireless Network?
In this modern world of fast-moving technology and handheld devices, it seems impossible to function properly without access to wireless internet. People all over the world from all walks of life rely on this wireless communication or Wi-Fi to complete their daily tasks and goals. From entertainment to business all things are done with the help of the wireless internet.
Critical Requirements for Mobile Security
0:00 Opening
6:06 What is Zero Trust?
11:48 Zero Trust workforce on mobile devices
14:57 Enabling Phishing protection on mobile
26:10 Vulnerability management for devices and applications
33:05 Ability to hunt for threats on mobile
43:45 Critical capabilities for comprhensive security
45:20 Q&A
Interview with a Hacker How are Attackers Targeting Mobile Devices
What is CIFS?
CIFS (Common Internet File System) is a network protocol that allows clients to communicate with servers and access file sharing and print services as if they were stored locally. The CIFS protocol is a particular implementation -- or dialect-- of the file-sharing protocol SMB (Server Message Block). The Server Message Block protocol was released by IBM in 1983 that has since undergone several modifications to its functionality by Microsoft.
CIFS vs. SMB: What's the Difference?
CIFS and SMB are both Windows file-sharing protocols used in storage systems, such as network-attached systems (NAS). The key difference between CIFS and SMB is that CIFS is a dialect of SMB – a particular implementation of the SMB protocol. The CIFS protocol is now considered an outdated SMB dialect, with the newer SMB 2.0 and SMB 3.0 addressing many of the inefficiencies of CIFS.
Cybersecurity and Drones: How to Address the Security Threats
The Unmanned Aerial Systems (UAS) industry has become a massive technological playground worldwide. Their extensive applications make UAS very popular for the public and the private sector. Armed forces, agricultural industry, law enforcement, meteorological agencies, medical services, environmental companies, and oil refineries are but a few out of the excessive list of UAS users.
Analyzing the PwnKit local privilege escalation exploit
What do Linux vulnerabilities and natural disasters have in common? Something seemingly dormant can suddenly spring to life, exposing activity beneath the surface. Several days ago, a security researcher published a high-severity vulnerability named PwnKit that impacts most major Linux distributions. The scary part? It’s existed since May of 2009. Polkit is a component for controlling privileges in Unix-like operating systems and is included by default on most major Linux distributions.