Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
How to Secure Amazon RDS Access With an Identity-Aware Access Proxy
Databases are sensitive resources that need an additional layer of protection and security. Though database servers have built-in authentication and authorization mechanisms, they are not designed for cloud-based, multi-tenant access mechanisms. Managed databases such as Amazon RDS are accessed and administered by different personas with varying levels of access permissions.
SurveyMonkey talks with Snyk about developer security during hypergrowth
Many companies look to CISOs or compliance teams to manage security throughout software development. But this practice usually keeps security considerations separate from developers. CISOs can assign security tasks to developers, but if developers aren’t thinking about security regularly, those tasks may be overlooked.
Cloud Threats Memo: What We Can Learn From the Top 15 Routinely Exploited Threats of 2021
Have you ever wondered what vulnerabilities are exploited the most by threat actors? The answers you have been eagerly waiting for could be found inside a joint Cybersecurity Advisory (CSA) coauthored by the cybersecurity authorities of the United States (CISA), Australia (ACSC), Canada (CCCS), New Zealand (NZ NCSC), and the United Kingdom (NCSC-UK), plus the U.S. National Security Agency (NSA) and Federal Bureau of Investigation (FBI).
Is It Reasonable to Deploy a SIEM Just for Compliance?
Many organizations need to meet various compliance standards, and investing in a security information and event management (SIEM) solution can often help them reach that goal. But it worth the cost and effort to deploy a SIEM solution solely for compliance? Or is there a way to maximize the value of your SIEM by strengthening cybersecurity as well as achieving compliance? This article will help you answer those critical questions.
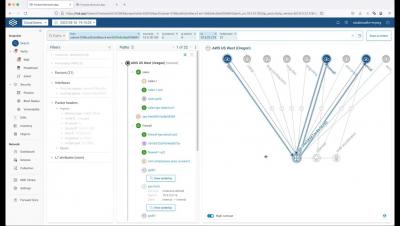
ONUG Spring 2022 Session: Verify security posture in hybrid multi-cloud environments
5 Key Considerations for Microsoft Teams Security
Microsoft Teams is a fantastic collaboration tool allowing people to share data effortlessly within the same organization and even across organizations. Unfortunately, because it was built with collaboration as the primary driver, it can be easy to ‘overshare’ data you don’t want to share.
AI in Cybersecurity - A Double-Edged Sword | Cybersecurity Sessions #7 with Elaine K. Lee
Generating an SBOM is just the tip of the iceberg
It has been nearly a year since the President Biden’s Executive Order 14028 catapulted Software Bills of Materials (SBOMs) from niche topic to the forefront of efforts to improve security of cyber supply chains. Since then not only have federal agencies including NIST and CISA delivered significant amounts of guidance and insight, but SBOMs have been the subject of intense debate across developer communities and beyond.
7 Important Things to Include in Your Company Security Policy
We live in risky times. Security incidents and data breaches are more common than ever and digital-minded companies usually bear the brunt of it. Organizations are constantly at risk and can be compromised in no time by ransomware, cyberattacks, social engineering, and corporate espionage. But, in truth, the most common way companies are undermined and infiltrated is through the actions of individual members inside of the organization itself.