Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Weekly Cyber Security News 03/06/2022
A selection of this week’s more interesting vulnerability disclosures and cyber security news. For a daily selection see our twitter feed at #ionCube24. A disturbing find, and how long before there is a rush by others to use this flaw?
How much money is spent on cybersecurity?
Businesses have never been more vulnerable than they are today. While cybercrime cost companies an already whopping US$300 billion in 2013, damages have since skyrocketed to US$945 billion in 2020. That’s 300% growth in just a short span of seven years. The worst part is, that we can expect this number to continue rising exponentially in the coming decade.
Truth in Malvertising?
Splunk SURGe recently released a whitepaper, blog, and video that outline the encryption speeds of 10 different ransomware families. Early in our research, during the literature review phase, we came across another group that conducted a similar study on ransomware encryption speeds. Who was this group you ask? Well, it was actually one of the ransomware crews themselves.
Introducing Mend Supply Chain Defender Integration with JFrog Artifactory
When it comes to understanding the difference between open source software vulnerabilities and malicious threats, it’s helpful to think in terms of passive vs. active threats. Vulnerabilities can be attacked and exploited, but in a vacuum don’t pose a threat. Malicious threats are different —– they involve a threat actor actively planning to attack you.
Amazon RDS Just-in-Time (JIT) Access With Teleport and Slack
This blog is part three in a series about secure access to Amazon RDS. In Part 1, we covered how to use OSS Teleport as an identity-aware access proxy to access Amazon RDS instances running in private subnets. Part 2 explained implementing single sign-on (SSO) for Amazon RDS access using Okta and Teleport. In Part 3, we will guide you through the steps to configure privilege escalation for just-in-time access requests for Amazon RDS access.
CVE-2022-26134 - Critical Vulnerability in Confluence Server & Data Center
We've joined the FIDO Alliance to build a better future for authentication
I’m happy to announce that 1Password has joined the FIDO Alliance to help build safer, simpler, and faster login solutions for everyone. In fact, we’re already on our way … keep reading for a sneak peek at the future of authentication in 1Password.
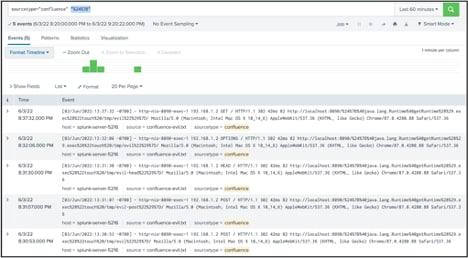
Detecting and mitigating CVE-2022-26134: Zero day at Atlassian Confluence
A new zero day vulnerability actively exploited in the wild has been found in Atlassian Confluence. The vulnerability CVE-2022-26134 affects all supported versions of Confluence Server and Confluence Data Center allowing an unauthenticated user to run arbitrary commands remotely. The Atlassian team confirmed the vulnerability with an official tweet and then also published a security advisory to update its customers.
Atlassian Confluence Vulnerability CVE-2022-26134
If you want just to see how to find evidence of the Atlassian vulnerability in your Confluence systems, skip down to the “detections” sections. Otherwise, read on for a quick breakdown of what happened, how to detect it, and MITRE ATT&CK mappings.