Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Snyk IaC for Terraform Enterprise: Expanding Snyk compatibility with HashiCorp Terraform
Even the most precise and regimented DevOps teams can be plagued by numerous post-deployment security issues, causing potentially damaging production delays and engineering rework. Building on Snyk’s successful acceleration of DevSecOps, Snyk IaC empowers developers to treat Terraform like any other form of code and proactively test IaC early as well as continuously monitor infrastructure post-deployment.
Introducing the new Snyk UI
Starting October 12th, 2022 we’ll be rolling out some exciting new user interface changes for the Snyk application, at app.snyk.io. These changes make use of the Snyk design system by incorporating standardized UI components, an updated color palette, and other elements to help you get even more from Snyk. In this blog post, we’ll walk through the most important changes.
Cloud SIEM Troubleshooting
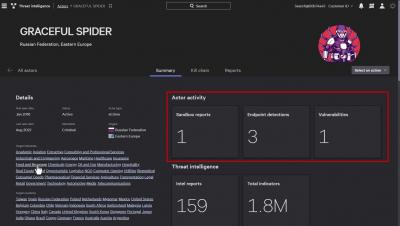
CrowdStrike Store - Falcon Intelligence
Introduction to OWASP's Vulnerable Node.js Apps: Part 1 | Snyk
Stranger Danger: Your Java Attack Surface Just Got Bigger
Machine Learning in Security: NLP Based Risky SPL Detection with a Pre-trained Model
The Splunk Vulnerability Disclosure SVD-2022-0604 published the existence of an attack where the dashboards in certain Splunk Cloud Platform and Splunk Enterprise versions may let an attacker inject risky search commands into a form token.
How to Securely Share Passwords with Third Parties Using Keeper
The popularity of freelancing has continued to rise in the United States. In fact, a majority of organizations in America have worked with freelancers and plan to hire them again, according to data from the LinkedIn Workforce Report. In the post-pandemic world, there are a massive and growing number of digital nomads, people who choose to travel while working remotely from anywhere in the Internet-connected world.
Protecting Healthcare Payments from Cyber Attacks: Tools and Strategies
In April 2022, a medical billing company based in New York became the victim of a serious ransomware attack. Bad actors stole personal and financial data of patients from 26 healthcare institutions who were the company’s clients. The billing company had to notify almost 1 million individuals that their data had been stolen. Over the last few years, organizations and fintechs that process payments for healthcare providers have become a hot target for cyber attacks.