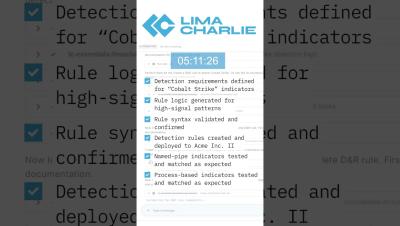
Detecting silent sensors: Identifying EDR telemetry gaps with LimaCharlie
One of the most insidious security risks isn't a sophisticated attack, it's the endpoint that stops reporting. A sensor that appears enrolled but hasn't sent telemetry in hours or days represents a critical blind spot. Whether due to network issues, system shutdown, agent crash, or intentional tampering, these silent sensors deserve immediate attention.