Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Bridging Network Security Gaps with Better Network Object Management
Prof. Avishai Wool, AlgoSec co-founder and CTO, stresses the importance of getting the often-overlooked function of managing network objects right, particularly in hybrid or multi-vendor environments.
Cricketer To Building A $8M ARR Security SaaS Platform! ft Ashish Tandon, Founder & CEO, Indusface
#BigPictureCyber Town Hall With MJ Thomas, Head of Cybersecurity, GD Bath Iron Works | 4/13/22
What is SOC 2?
Westcon-Comstor to add EfficientIP solution to its distribution portfolio in Europe, Africa and Asia-Pacific
Protecting your Microsoft 365 services against NOBELIUM attacks [E-book]
In December 2020, Microsoft came forward with details regarding what is now being considered the most extensive, severe cyberattack in history—the NOBELIUM attack. This shocking security breach by NOBELIUM, a group of Russian hackers, brought the cybersecurity world to a standstill with its well-planned and well-executed hacking. It compromised several organizations through a supply chain attack.
Netacea Receives Top Score in Bot Detection Criterion in 2022 Analyst Report
Data is Everywhere and Encryption Must Follow: Why You Need EDRM
It is becoming increasingly difficult to guarantee a safe boundary for your sensitive data. As work-from-anywhere cements, employees are now collaborating freely with each other, with contractors and with partners. But this freedom to collaborate more broadly also means information is being shared among devices, applications and networks that your organization doesn't necessarily have control over.
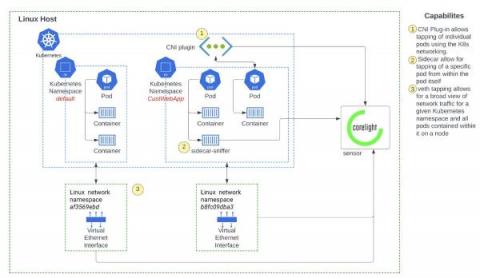
Deeper visibility into Kubernetes environments with network monitoring
Network monitoring solutions can overcome the security visibility blind spots in Kubernetes environments, by providing a source of truth for SOC analysts. Container security solutions broadly span the spectrum of (a) prevention - securing the container image and ensuring the right policies are in place during runtime and (b) detection - monitoring runtime events for threat detection and investigation.