Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
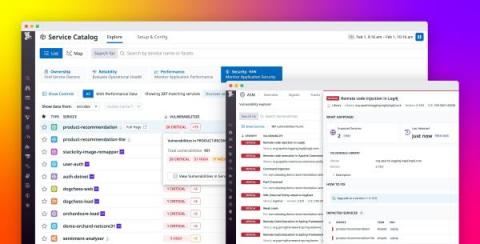
Gain visibility into open source vulnerabilities with Datadog Application Risk Management
Open source libraries have become an indispensable part of modern applications. Approximately 90% of organizations use open source software to support their services, but monitoring these dependencies can be difficult when environments run thousands of ephemeral services. The complex nature of modern applications, in combination with the challenge of keeping a competitive edge in a fast-moving market, can make it difficult for organizations to identify and remediate threats in a timely manner.
How to Measure Cyber Risks in Healthcare
Cyber risks are prevalent in all healthcare institutions, and understanding how to mitigate those risks is especially important in today’s cyber landscape. Cyber risk is the sum of all IT risks that can potentially lead to the loss or exposure of critical data, financial damages, reputational damages, and operational stoppages due to a data breach or data leak. Measuring cyber risks involves determining the likelihood and impact of each cyber threat.
Why is Cyber Incident Reporting Important?
Because cyber threats continue to grow in sophistication and effectiveness, cyber incident reporting is not only important but also necessary for other organizations to learn from and prevent making the same mistakes. Many governing bodies and federal governments around the world have begun to require cyber incident reporting to document the type of attacks used, the source of the attacks, and how the attacks occurred to better understand the threat landscape.
Cyber Security Decoded feat. Wendi Whitmore | Episode 1
Adi Sharabani, Snyk CTO On Adapting to Change: The Future of Security in a DevSecOps World
A Day In The Life of A CISO - Prajal Kulkarni - CISO - Groww
What Is Business Profile Hijacking & How You Can Protect Your Business
Search engines automatically create a business listing based on publicly available information, but they permit business owners to override this automatic listing by publishing their own. This listing may include business hours, slogan, geographical location, a website link, contact information, reviews, and images. Business owners are also permitted to respond to reviews. Recently, Sedara has seen incidents in which the attacker claims control over a business listing that they do not own.