Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
CloudCasa Certified OpenShift Operator Installation Demo
Why CloudCasa is the Best Choice for Backup and Recovery of Red Hat OpenShift
Red Hat® OpenShift® Container Platform (OCP) is an enterprise-grade Kubernetes platform for building, deploying, running, and managing containerized applications in a hybrid world. The reality is that with Red Hat OCP, building, deploying, running, and managing containerized workloads couldn’t be any easier.
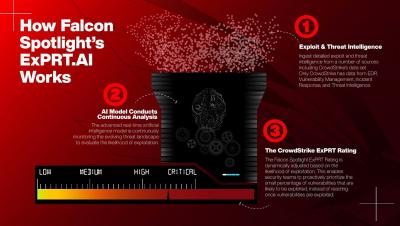
How to Use Falcon Spotlight's ExPRT.AI
Detect & Mitigate Your Ransomware Risk with Egnyte
Introduction to Custom Fields
Netskope Cloud Exchange
Netskope - The Undisputed Leader in the Evolution of CASB and Cloud Security
Cloud Access Security Brokers (CASB), also known as Cloud Security Gateways, were created to address the increasing cloud security problems facing organizations as cloud and application usage increased over the last decade.
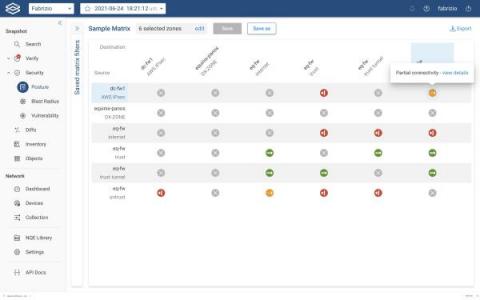
Where is Your Zone-to-Zone Connectivity Matrix?
If you’re like most of the complex IT shops we talk with, you probably don’t even have a current security matrix to store anywhere – file cabinet or data folder. The connectivity matrix is essentially the company security posture, but almost no one has a comprehensive way to visualize and easily understand the connectivity status between the various configured security policies (zone-to-zone policies).
ISO 27001 Compliance: What You Need to Know for Your Certification
Looking to become certified to the ISO 27001 standard? In this article you will learn what ISO 27001 is, the key terms and definitions, information security risks you need to consider, and the process for meeting your compliance and certification requirements.