Enrich Your IPAM Data with Our Certified Infoblox NIOS Integration
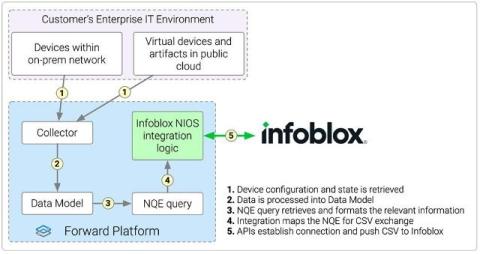
Keep Your IPAM Data Accurate, Complete, and Always Up to Date With our certified integration, Forward Enterprise delivers reliable, always-up-to-date network data straight to Infoblox NIOS.