Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Supply Chain Security, Compliance, and Privacy For Cloud-Native Ecosystems
Netskope Private Access Demo - Browser Access (Clientless)
Netskope Selected to Participate in ATARC Zero Trust Lab
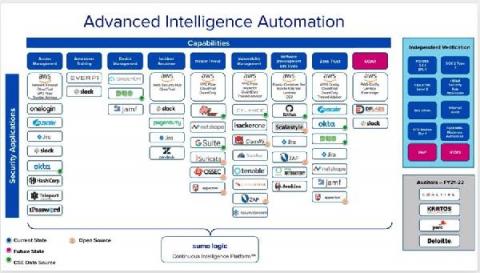
We are pleased to share that Netskope has been selected by the Advanced Technology Academic Research Center (ATARC) as one of 49 vendors to participate in its Zero Trust Lab. The Zero Trust Lab is a state-of-the-art physical and virtual test environment that will provide federal agencies with the opportunity to build, test, and evaluate new Zero Trust Architectures in a simulated environment.
.NET 5, Source Generators, and Supply Chain Attacks
Attacks executed through builds abuse trust we have in our build tools, IDEs, and software projects.
Devo Content Stream
Secret backdoor allegedly lets the REvil ransomware gang scam its own affiliates
REvil is one of the most notorious ransomware groups in the world. Also known as Sodin and Sodinokibi, REvil has made a name for itself extorting large amounts of money from businesses, operating as a ransomware-as-a-service (RAAS) business model that sees it share its profits with affiliates who break into networks and negotiate with victims on the group’s behalf.
Introducing Egnyte's Monthly Release Rollups
We’re kicking off a new series that will roll up our most recent product releases you need to know, all in one place. This first post will summarize some of the releases from the last few months. Moving forward, expect to see a post each month. We’re excited to share all the new features and product improvements we’ve been working on with you, so you can make the most of the Egnyte platform.
Investigating GSuite Phishing Attacks with Splunk
Malicious actors are constantly finding new ways to deliver their malicious payloads. With the recent migration of businesses moving to web application-based services, file storage, email, calendar, and other channels have become valuable means for delivering malicious code and payloads. In some instances, these services are abused as Command and Control infrastructure since many enterprises trust these services by default.
The Importance of Prioritizing Product Security
Achieving comprehensive security for the products delivered and deployed by organizations is becoming more difficult, due to a variety of factors. A key one is the growing volume, variety and complexity of software and connected devices in use. Another is the overwhelming risk of inherited software supply chain exposures. The result: Companies struggle every day to provide software with optimal security and protection against malicious activities, takeovers, data theft, and commercial sabotage.