Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Announcing: Code-free API log collection and parser creation
AT&T Cybersecurity is pleased to announce a code-free way for our USM Anywhere customers to make their own API-driven log collectors and custom parsers. This big advancement in threat detection and response technology will make it possible for customers to collect information from a much larger variety of sources and SaaS services without having to request new integrations or log parsers.
How SIM card registration with ID Biometrics is revolutionizing telecom security in Lesotho, Namibia
The southern African nations of Lesotho and Namibia have newly begun programs for users to re-register their SIM cards with their biometrics and digital IDs, adding them to the list of newly joined countries adapting to the new norms in Africa. South Africa is also set to schedule biometric SIM registration, with further plans to push ‘ID4Africa’ as a type of incentive-based identity enrollment approach for governments.
Stranger Danger: Your Java Attack Surface Just Got Bigger
The Anatomy of Wiper Malware, Part 2: Third-Party Drivers
In Part 1 of this four-part blog series examining wiper malware, we introduced the topic of wipers, reviewed their recent history and presented common adversary techniques that leverage wipers to destroy system data. In Part 2, CrowdStrike’s Endpoint Protection Content Research Team discusses how threat actors have used legitimate third-party drivers to bypass the visibility and detection capabilities of security mechanisms and solutions.
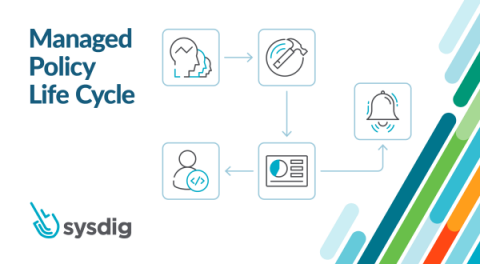
Introducing Managed Policies for Sysdig Secure
Whether you’re learning cloud-native workload protection for the first time or running all your microservice workloads in production, you probably already noticed that cloud-native security is much different from security design used for traditional monolith applications. The dramatic increase in complexity and the evolving threat landscape make cloud and container security even more critical and harder to manage.
8 tips for securing containers from source to runtime
Today we’re announcing a new container security cheat sheet and report — created in collaboration with our partner Sysdig. Download cheatsheet In this post, we’ll outline tips to help you successfully navigate the challenges of container security with a focus on three core principles: Traditional security approaches are incapable of handling the distributed and ephemeral nature of containers.
When Should You be Using Encryption?
Hats Off to Black Hat USA 2022 in Vegas
For its 25th year, Black Hat USA presented a “unique hybrid event experience, offering the cybersecurity community a choice in how they wish to participate” virtually or in person. It was a jam-packed four days of trainings, conferences, briefings, special events, and cybersecurity solutions.