What is Adaptive Threat Protection?
According to McAfee, Adaptive Threat Protection (ATP) is an endpoint security’s optional module that analyzes organizational content and decides action based on file rules, reputation, and reputation thresholds. According to another source, the ATP is a security model that monitors threats, improves cybersecurity risks changes, and evolves to meet the need for security systems that are integrated with IT for continuous deployment, as well as in hybrid environments and the virtual cloud.
How to Prevent Industrial Espionage
Every organization needs to keep tabs on other players in the industry in order to stay competitive. It’s common for an organization to analyze a competitor’s website, perform secret shopping trips, and monitor a competitor’s marketing strategies. This type of competitive research is perfectly legal. But if an organization unlawfully obtains another company’s sensitive information, it is considered industrial espionage, which is illegal.
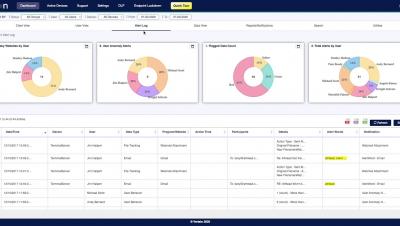
Veriato Vision UI Overview
MITRE ATT&CK July 2020 Update: Sub-Techniques!
The highly anticipated structural update to the MITRE ATT&CK framework was released July 8th, 2020. After a quiet first half of the year, it appears the ATT&CK team has been putting in lots of work into some significant redesign of the framework’s structure. This update introduces a new layer of abstraction: sub-techniques.
Cosmic Lynx: The Highly-Professional Cybercrime Gang Scamming Businesses Out of Millions of Dollars
Things just got serious. Business Email Compromise is no longer solely the province of chancers and opportunistic Nigerian actors such as the Yahoo Boys. Organised criminal gangs with a high level of professionalism have seen the opportunity and seized it. Security researchers at Agari have published a report detailing their investigations into a Russian cybercrime gang they say have stolen millions of dollars from companies in 46 countries since mid-2019.
macOS vs. Windows - What kernels tell you about security events: Part 2
This post continues this two-part blog series on further understanding the differences between macOS and Windows on the system level for effective endpoint security analysis. In Part 1, we covered process events. Here in Part 2, we’ll discuss file and network events. As with Part 1, my hope is to help cybersecurity professionals expand and enrich their experiences on a less familiar platform, ultimately helping them to be better prepared to face differences from past experiences.
Introducing Teleport 4.3 - Modern Replacement for OpenSSH
We’re excited to announce the release of Teleport 4.3 - new UI, API driven, expanded audit capabilities, and still open source. This version is so significant, we nearly called it 5.0! In this post, we’ll cover the major new features and you’ll see why we called it ‘Teleport’.
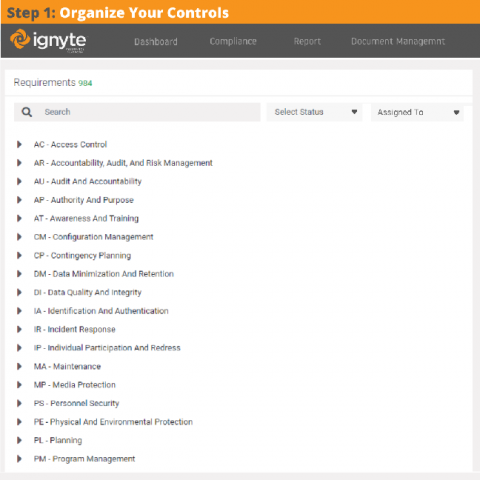
Collect Evidence & Artifacts from people with Request Links
Controls management and assessments are critical for properly managing a complete information security program. Similarly, evidence collection, management, and approval is vital for proper control based security governance programs in any organization.
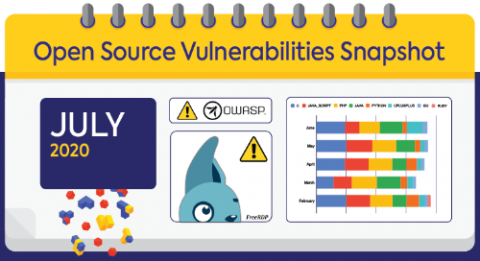
July 2020 Open Source Security Vulnerabilities Snapshot
Now that the sparkle and pop of the Fourth of July’s fireworks has subsided, it’s time for July’s open source vulnerabilities snapshot, your monthly overview of everything new in the always-evolving world of open source security.