The Biggest Breaches and Data Leaks of 2020
Year after year, cyberattackers cause unnecessary stress for organizations, disrupting innovation and impacting profit. 2020 was no different – last year brought a bevy of damaging breaches that cost organizations precious money and time they couldn’t get back. Ranging from thousands to billions of records exposed, breaches big and small gave threat actors access to sensitive information like email addresses, locations, passwords, dates of birth, and more.
Protecting Your Electronic Health Records (EHR) With Continuous Monitoring
After a year of lockdown, or nearly full lockdown, due to the ongoing health crisis, we learned a lot from how our organizations responded when we all had to change our work habits to a home-office setup.
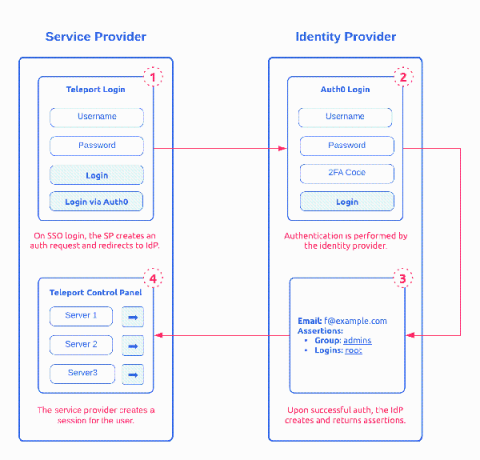
How SAML 2.0 Authentication Works?
Security Assertion Markup Language (SAML) 2.0 is one of the most widely used open standard for authentication and authorizing between multiple parties. It’s one of the protocol that give users the single sign-on (SSO) experience for applications. The other adopted open standard is OAuth and OpenID. Of the two, SAML 2.0, released in 2005, remains the 800 pound gorilla in Enterprise SSO space. This post provides a detailed introduction on how SAML works.
Cloud Threats Memo: LinkedIn Spearphishing and Malware-as-a-Service
‘More_eggs’ is a backdoor sold as a “malware-as-a-service” (MaaS) by a threat group known as “Golden Chickens” and predominantly used by three criminal groups: FIN6, Cobalt Group, and Evilnum. In the latest campaign, unearthed by researchers from eSentire and targeting a professional working in the healthcare technology industry, a threat actor is exploiting fake job offers on LinkedIn to deploy the ‘More_eggs’ backdoor on the victim’s machine.
Endpoint Security Data Collection Strategy: Splunk UF, uberAgent, or Sysmon?
Many threats originate from the endpoint and detecting them requires insights into what happens on the endpoint. In this post we look at different endpoint activity data sources, comparing the benefits and capabilities of Splunk Universal Forwarder with vast limits uberAgent and homegrown solutions.
Advanced mobile protection through the AlienApp for MobileIron
Companies of all sizes need clear and cohesive security visibility over every aspect of their organization. As data and assets are trending to mobile, it’s critical to be equipped with the right tools to gain insights on mobile devices and users on the endpoints and mitigate threats whenever needed.
Insider Threat Awareness: What Is It, Why Does It Matter, and How Can You Improve It?
Sharing Activeboards
Unveil hidden malicious processes with Falco in cloud-native environments
Detecting malicious processes is already complicated in cloud-native environments, as without the proper tools they are black boxes. It becomes even more complicated if those malicious processes are hidden. A malware using open source tools to evade detection has been reported. The open source project used by the malware is libprocesshider, a tool created by Sysdig’s former chief architect Gianluca.