IT analytics in 90 seconds: Monitor disk encryption to prevent data theft
White House Memo Takes on Securing Critical Infrastructure Control Systems
Attacks targeting critical infrastructure have been on the rise in recent years. Back in 2019, for instance, 56% of utility professionals responsible for overseeing risk in their organizations’ operational technology (OT) assets told Siemens and the Ponemon Institute that they experience at least one shutdown or operational data loss event a year.
Are vulnerability scan reports dangerous?
Vulnerability scan reports are requested from a wide variety of people or entities for many different reasons. Historically a report meant a static snapshot of the scan data. Some company stakeholders may want an executive overview of the current vulnerabilities present in their environment. In contrast, others may want additional data points such as trending to reflect how well they have made progress in remediating previous vulnerability scans detected.
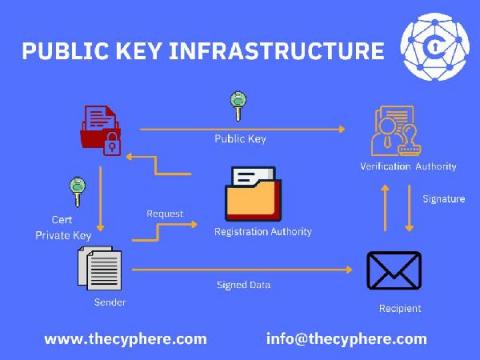
Public Key Infrastructure: PKI explained in simple terms
PKI stands for Public Key Infrastructure. It is the foundation of modern information security. PKI is a set of practices, policies, and technologies that protect sensitive data from unauthorised access or use. If you’re not using it yet, there are many reasons why you should be.
Threat Intelligence Management - the Foundational Use Case for a TIP
I previously talked about how to get started with a threat intelligence program, which is the cornerstone to any security operation. Such a program enables security teams to gain a deeper understanding of adversaries and their tactics, techniques and procedures (TTPs), in order to determine what is relevant to the organization and how to mitigate risk.
Product Update: Detectify fuzzing engine will cover public-facing APIs
Detectify is expanding its web app fuzzing engine to scan public-facing APIs for vulnerabilities. Earlier in the year, we released a new fuzzing engine, and it was developed with API scanning in mind. In Fall 2021, we will roll out open beta testing. You can register for Detectify API fuzzer updates and beta testing program.
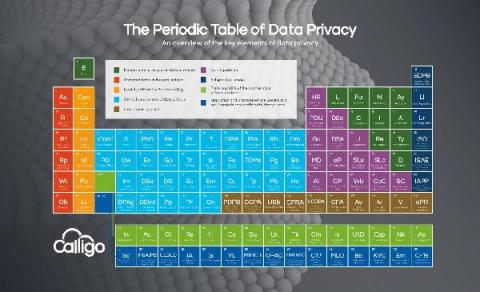
UPDATE 7: The Data Privacy Periodic Table
Since our last update in January, there has been an unprecedented amount of activity in the data privacy world. And yes, we probably do say that every time! New laws have passed in Virginia and Colorado. The UK’s post-Brexit EU adequacy was confirmed. Plus of course, the EU’s significant changes to Standard Contractual Clauses and the reawakening of the debates over Identity Verification, especially in the context of social media.
Limitless XDR defined: Ingest, retain, and analyze security data freely
Elastic Security's newest features define the potential of XDR for cybersecurity teams. Our single platform brings together SIEM and endpoint security, allowing users to ingest and retain large volumes of data from diverse sources, store and search data for longer, and augment threat hunting with detections and machine learning. Security vendors are using the term “XDR” with increasing frequency, applying varied definitions to suit their respective technologies.