What is Cyber Resilience?
Since the covid-19, the cyber incident ratio has drastically increased and shows no signs of settling down. In just one year, cyber-attacks have targeted big enterprises, government agencies of the world’s leading countries, educational institutes, non-government organisations (NGOs), and small to mid-sized businesses. It is estimated that threat actors carry out cyber attacks every 39 seconds, which is relatively faster than before.
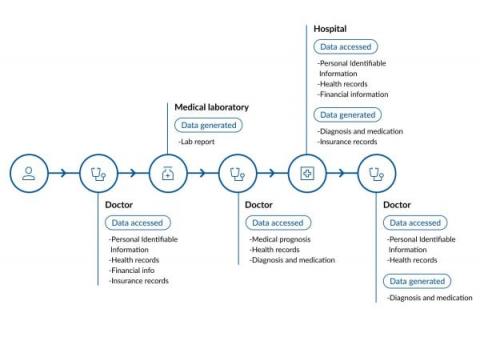
Big Data challenges in tele-healthcare
Covid-19 pushed the boundaries of both healthcare and technology providers, and nudged people to finally embrace telehealth services. In fact, telehealth has proven to be the next frontier for the healthcare industry as it minimizes the need for in-person patient, clinic, or hospital visits which prevents overwhelming our healthcare systems. A McKinsey report shared that the use of telehealth in the US in 2021 surged 38 times compared to pre-pandemic levels.
Applying Least Privilege in Kubernetes II Jonathan Canada
Why the United States Federal Government Considers Ransomware a Critical Risk to Business
At the Rubrik Data Security Summit, leaders from both the public and private sectors discussed an important topic: ransomware. Cyber threats continue to expand in both volume and sophistication with attacks growing at a rate of 150% annually. As attackers increasingly target backups, it will be even more paramount for policies and guidance from government agencies to match the security innovation of private sector businesses to mitigate the risks of this cyber pandemic head-on.
How to better secure user authentication protocols
In March 2021, cybersecurity researcher Le Xuan Tuyen discovered a security bug in Microsoft Exchange Server. The vulnerability, dubbed ProxyToken, lets attackers bypass the authentication process to access victims’ emails and configure their mailboxes.
How secure is your Zendesk instance? Find out with Nightfall's Zendesk DLP scanner
When your customers reach out for help, they send messages to your support team that likely contain personal information. Help desk ticketing systems can often harvest for personally identifiable information (PII) like email addresses and credit card numbers, while healthcare providers using ticketing systems may request protected health information (PHI) like patient names and health insurance claim numbers or phone numbers.
Is Teamviewer safe? Experts & Real Users Answer
You may have previously heard about TeamViewer if you’ve ever needed to remotely access another device for the purposes of maintenance or general work activities.
An Introduction to the Snyk Team pricing plan
The Vulnerability Conundrum: Improving the Disclosure Process
The vulnerability disclosure process involves reporting security flaws in software or hardware, and can be complex. Cooperation between the organization responsible for the software or hardware, and the security researcher who discovers the vulnerability can be complicated. In this blog we’ll look at the vulnerability disclosure process, the parties involved and how they can collaborate productively.