New CCO's Mission: Create a World-Class Experience for Devo Customers
Johannes Loeffler recently joined Devo as chief customer officer. He and his worldwide team are responsible for accelerating Devo’s efforts to provide customers with a seamless and superior customer experience. I joined Devo because I saw an amazing company with huge potential that is disrupting the logging and SIEM market. Devo’s solutions and services provide incredible value to our customers. And our customers are loyal to us, which is something money can’t buy.
5 Common Cybersecurity Vulnerabilities in the IoMT
Have you been to the hospital lately? If so, you’ve probably been attached to at least one medical device with at least some sort of internet access. According to Cisco, the average hospital room has, on average, 15-20 connected devices, with an average of 6.2 cybersecurity vulnerabilities between them.
Welcome to Nightfall's Engineering Blog
From our beginnings as childhood friends to coming up together in the tech industry, Isaac and I would catch up on our adventures as professionals working in Silicon Valley: him in the VC world, and me as an engineer at Uber Eats. We’re both very interested in entrepreneurship, so we would always come back to discussing various business ideas, including a topic we’d both become intrigued with — the existing challenges enterprises faced with cloud data security.
Infosec for startups
6 Business functions that will benefit from cybersecurity automation
Enterprises and small businesses alike are facing challenges that impact their ability to maintain adequate cybersecurity. Budget constraints and limited staff are just a couple of reasons why businesses have become more susceptible to cyberattacks. Hackers are becoming smarter, and the tools that teams deploy are growing in number, leading to fragmentation and increased vulnerabilities.
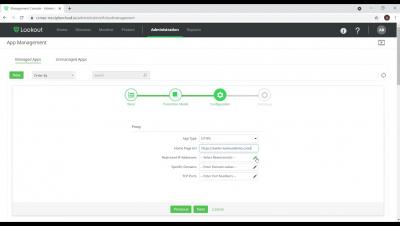
Lookout ZTNA - Intro to onboarding an application, securing access and protecting sensitive data.
Supply Chain Shock: Realities About the Security of the Software Supply Chain
News reports on attacks on the “supply chain” are becoming an almost every-day occurrence. First there was SolarWinds, then Kayesa, followed by countless other large and small supply chain attacks. Global businesses, economies, and lives are intricately connected to each other through applications and the internet. When critical systems are attacked and operations are affected, the downstream problems quickly become apparent.
Securing legacy systems and protecting your Data
If you ask the question “who is responsible for a company’s cybersecurity,” the answer you’ll most likely hear is no longer the CTO, or the IT department, but instead the CEO. In fact, Gartner believes that 75% of CEOs will be held personally liable for cyber and physical breaches by 2024. That means there’s no more passing the buck on this complex issue.
What You Need to Know About Code Risk Management
Risk management of code is an important and often overlooked development function that you need to pay attention to. You may think that this is not a developer’s problem, however developers should not write code that unduly adds to technical debt, hence the need to manage risk. The primary motivation for risk management is to prevent error or failure. Do not seek to eliminate failure, seek to minimise it, to manage the risk of failure.