Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Automated Developer-First Security: Our Partnership with Snyk
Today’s developers move at increasingly rapid speed – making it more critical than ever to identify and resolve code vulnerabilities early in the software development lifecycle. By tackling security early – instead of waiting until testing and deployment – engineering teams can reduce unnecessary patching and maintenance cycles, reduce risks, and ensure timely delivery of new features.
7 Cybersecurity Best Practices Financial Firms Should Live By
Suspicious behavior: OTX Indicator of Compromise - Detection & response
AT&T Alien Labs does a tremendous job of developing and maintaining a database of observed Indicators of Compromise (IOC) that have been involved with at least one customer through the Open Threat Exchange (OTX).
5 Common Ways You're Putting Your Company's Cybersecurity at Risk (and How to Do Better)
How to Automate Intune Device Reports with Torq
Whether for managing remote teams, supporting ‘bring your own device’ (BYOD) policies, or simply another layer in a data protection strategy, services like Microsoft Intune offer greater control over the devices on your network. But using the data from these services often requires tedious prep work, and this process is likely repeated multiple times a week, if not daily. Tedious, repetitive, structured: these are all signs that a process can and should be automated.
Outsourcing your SOC
With businesses constantly at risk of cyber threats, leveraging a Security Operations Centre (SOC) is one way for organisations to proactively monitor and manage their threat landscape. Whether it’s in-house or outsourced, a SOC can help companies implement a process-driven security framework that secures business information against the constant threat of a cyber attack.
How Legal Organizations Can Address The Evolving Threat Landscape
Critical Authentication Bypass Vulnerability in VMware Products - CVE-2022-22972
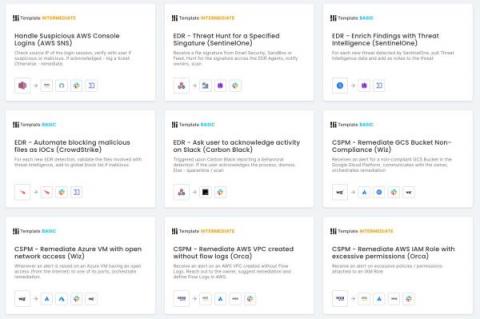
Latest Features Enhance Workflow Creation, Add Modern Controls
The consensus on the state of cybersecurity professionals tends to fall somewhere between “burdened by high volumes of responsibility” and “dangerously understaffed and suffering from unhealthy levels of stress,” depending on how optimistic your source is.