Networks
Top F5 WAF Alternatives in 2023
Networking and Security Teams Are Converging, Says SASE Adoption Survey
Converging networking with security is fundamental to creating a robust and resilient IT infrastructure that can withstand the evolving cyber threat landscape. It not only protects sensitive data and resources but also contributes to the overall success and trustworthiness of an organization. And just as technologies are converging, networking and security teams are increasingly working together.
Healthcare IT: Improving Patient Care and Satisfaction with SD-WAN
The phrase “digital transformation” gets thrown around a lot these days when discussing IT infrastructure. A popular — albeit slightly vague — buzzphrase for a reason, digital transformation, in this context, simply refers to the idea that businesses are working to modernize their operations and leverage the power of new technologies.
Forward Networks Named Outperformer in GigaOm Radar for Network Validation for Second Consecutive Year
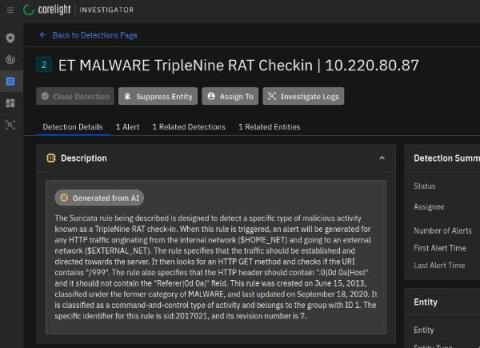
Turning the tables on the infiltrator
What happens at the point in time when an organization’s information security is compromised? This blog explores an important paradigm shift that occurs at the very moment of compromise and that can be leveraged to turn the tables on the attackers.
Disable LLMNR for Network Security
Put Cloud in the Fast Lane: Why SD-WAN
If routing traffic on your network, managing cloud-based software-as-a-service (SaaS) applications, or general cloud connectivity is becoming more difficult for your IT team to manage, you may be ready for a software-defined wide area network (SD-WAN). SD-WAN is powerful networking tool that can help you centrally manage your traffic flow, independent of the underlying hardware on your network.
Black Hat NOC USA 2023: Five takeaways for SOC teams
During this year’s Black Hat in Las Vegas, I learned (or was reminded of) many lessons working alongside my Corelight colleagues and Black Hat Network Operations Center (NOC) teammates from Arista, Cisco, Lumen, NetWitness and Palo Alto Networks. The uniqueness of standing up a full security stack and NOC in such a short time with a team that comes together infrequently really forced me to consider how team processes and communication affect NOC/SOC efficiency and effectiveness.