Networks
Turning the tables on the infiltrator
What happens at the point in time when an organization’s information security is compromised? This blog explores an important paradigm shift that occurs at the very moment of compromise and that can be leveraged to turn the tables on the attackers.
Disable LLMNR for Network Security
Put Cloud in the Fast Lane: Why SD-WAN
If routing traffic on your network, managing cloud-based software-as-a-service (SaaS) applications, or general cloud connectivity is becoming more difficult for your IT team to manage, you may be ready for a software-defined wide area network (SD-WAN). SD-WAN is powerful networking tool that can help you centrally manage your traffic flow, independent of the underlying hardware on your network.
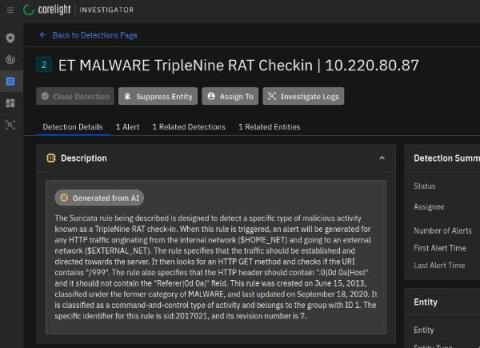
Black Hat NOC USA 2023: Five takeaways for SOC teams
During this year’s Black Hat in Las Vegas, I learned (or was reminded of) many lessons working alongside my Corelight colleagues and Black Hat Network Operations Center (NOC) teammates from Arista, Cisco, Lumen, NetWitness and Palo Alto Networks. The uniqueness of standing up a full security stack and NOC in such a short time with a team that comes together infrequently really forced me to consider how team processes and communication affect NOC/SOC efficiency and effectiveness.
Fireside Chat: Leading Global Security and Network Transformation
Cato's Analysis and Protection for cURL SOCKS5 Heap Buffer Overflow (CVE-2023-38545)
TL;DR This vulnerability appears to be less severe than initially anticipated. Cato customers and infrastructure are secure. Last week the original author and long-time lead developer of cURL Daniel Stenberg published a “teaser” for a HIGH severity vulnerability in the ubiquitous libcurl development library and the curl command-line utility. A week of anticipation, multiple heinous crimes against humanity and a declaration of war later, the vulnerability was disclosed publicly.
5 Reasons Why VPN is an Essential Utility for Internet Users
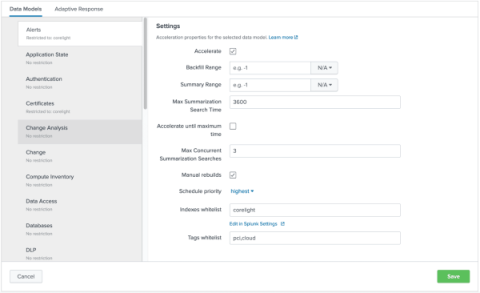
Enhance your search experience within Splunk by using the Corelight App
The Corelight App for Splunk provides the foundation for organizations to boost SOC effectiveness and productivity by using Corelight data in Splunk. In this blog, I’ll walk through how the Corelight App leverages Splunk’s Common Information Model (CIM) to enhance users' search experience when they are using Corelight data.