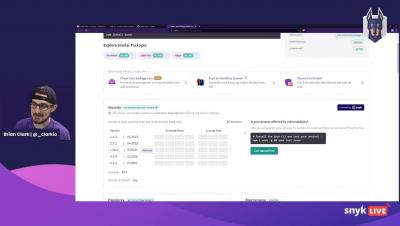
Monthly JFrog Xray Demo
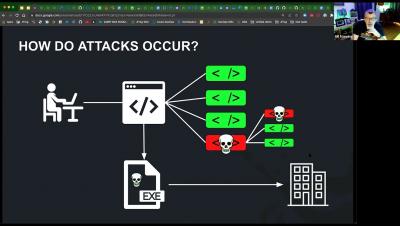
William Manning, JFrog Solutions Engineering Manager, hosts "Monthly JFrog Xray Demo." See how Xray provides intelligent supply chain security and compliance at DevOps speed. JFrog Xray is a software composition analysis (SCA) solution that scans your open source software (OSS) dependencies for security vulnerabilities and license compliance issues.