Software Supply Chain Security for Open Source Projects
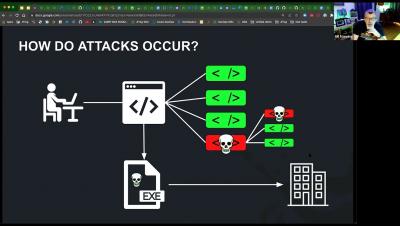
Attacks on the open-source value chain (OS supply chain) are becoming more sophisticated, and we, as software developers, are becoming the focus of these attacks. So what are the essential first steps, and what should you focus on? This raises the question of suitable methods and tools. At the same time, the company's strategic orientation must be considered in this security strategy. In the recent past, we have also learned that attacks are increasingly targeting individual infrastructure elements of software development, such as the classic CI/CD pipeline.