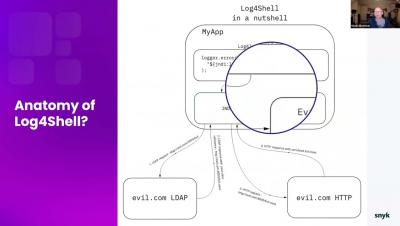
Log4Shell Live Hack: A Hands-on, Actionable Fix Guide
In this live hack webinar on the Log4Shell exploit we give a brief overview of the vulnerability and dive right into some examples of the exploit in action. We then show several real-world remediation approaches as well as other fixes outside of code. We feature a final round of fun demos, including container and IaC hacks and Java-based game hacks. We wrap up with a great list of takeaway resources and answer your questions.